
Sophisticated ransomware and a Cuba-Russia link
How does Bughatch, the sophisticated backdoor that cleverly hides in process memory, work? Specifically, it executes an embedded block of shellcode (a string of characters that represents executable binary code), interacting with the Windows API and connecting to a command and control (C2) server waiting for instructions. This backdoor is capable of downloading malware such as Cobalt Strike Beacon and Metasploit. The use of Veeamp suggests strong Cuban involvement in these attacks.Let's then talk about the term "komar", found in the PDB file. This refers to the Russian word “mosquito”, which suggests a possible presence of Russian-speaking members within the Cuba group, which could make you smile. Further analysis by Kaspersky researchers revealed other modules used by Cuba to improve the functionality of the malware. One of these modules collects system information, transmitted to a server by HTTP POST requests.
Experts have identified new malware samples attributed to Cuba, evading advanced detection by some security vendors. These samples represent recent iterations of Burntcigar malware, which uses encryption to evade antivirus detection.
Malware is particularly difficult to detect, and that's the whole problem
As it stands, cyber specialists emphasize the importance of staying at the forefront of threat reporting and intelligence as ransomware gangs like Cuba evolve rapidly and refine their tactics day by day. There's no mystery: As the cyber threat landscape continues to evolve, knowledge is the best defense against these emerging cybercriminal groups.
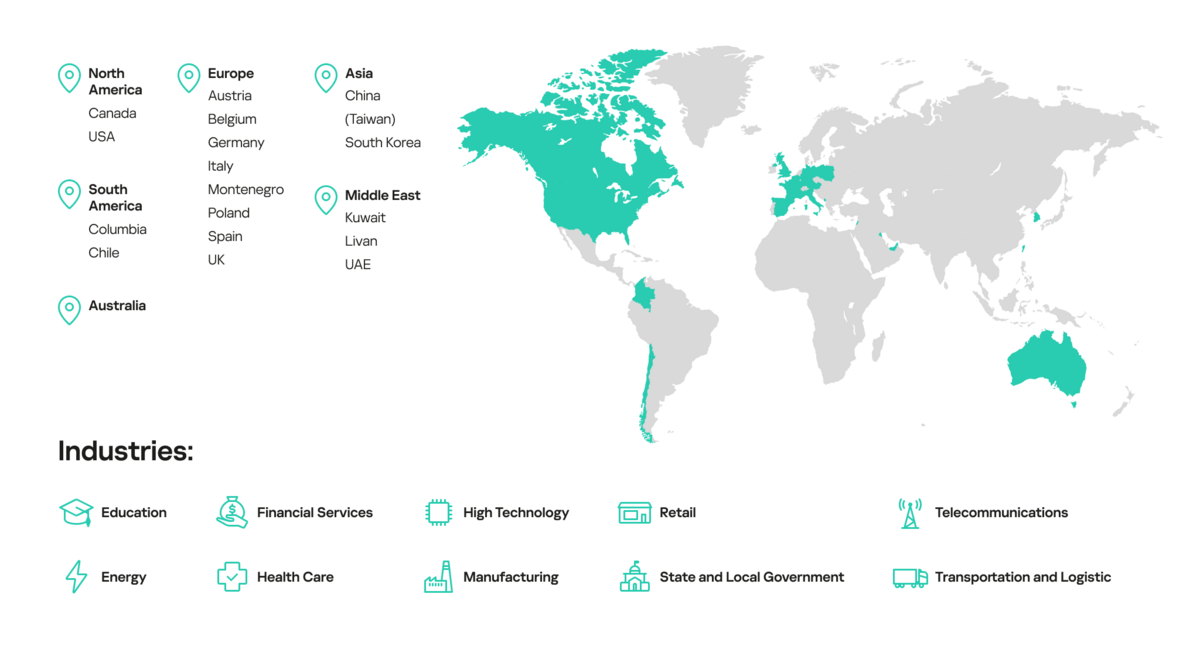
The trouble is that Cuba, as a single-file ransomware strain, is particularly difficult to detect. In fact, it doesn't need additional libraries, mind you. The Russian group targets a wide range of sectors, including retail, finance, logistics, government and healthcare agencies, and manufacturing, in various regions around the world. Among the countries concerned, we can cite France, certainly to a lesser extent than others such as Germany, the United States, Australia, China, the United Kingdom, and even Italy.
Cuba's malicious agents use a combination of public and proprietary tools, regularly updating their arsenal. They use tactics like Bring Your Own Vulnerable Driver (BYOVD) and alter timestamps to confuse investigators. Their unique approach not only encrypts data, but also aims to extract sensitive information, making software development companies particularly vulnerable. And even though Cuba has been the center of attention for some time, this group remains active and constantly perfecting their techniques.
How do you think mates !
