- Downloaded
- 135.2 GB
- Uploaded
- 13.1 TB
- Ratio
- 99.14
- Seedbonus
- 259,715
- Upload Count
- 265 (300)
Member for 9 years
[udemy] 2024 Network Defense Mastery: Techniques and Tools

MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Duration: 3h 24m | Size: 677.8 MB
Learn Identification, Controls, Virtualization, and Cloud Security.
What you'll learn
Understand and apply various network defense strategies.
Deploy and configure firewalls, IDS, and IPS systems.
Secure virtual and cloud environments effectively.
Implement strong cryptographic systems and PKI.
Enhance wireless network security with robust protocols.
Execute practical security projects using tools like Snort and VPNs.
And more...
Requirements
Basic computer skills
Interest in cybersecurity
No prior network knowledge required
Access to a computer with internet
Who this course is for:
IT professionals looking to specialize in network security.
Beginners interested in a cybersecurity career.
System administrators aiming to enhance their security skills.
Students studying computer science or related fields.
Business owners needing to secure their network environments.
Hobbyists and tech enthusiasts eager to learn about network defense.
Download

MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Duration: 3h 24m | Size: 677.8 MB
Learn Identification, Controls, Virtualization, and Cloud Security.
What you'll learn
Understand and apply various network defense strategies.
Deploy and configure firewalls, IDS, and IPS systems.
Secure virtual and cloud environments effectively.
Implement strong cryptographic systems and PKI.
Enhance wireless network security with robust protocols.
Execute practical security projects using tools like Snort and VPNs.
And more...
Requirements
Basic computer skills
Interest in cybersecurity
No prior network knowledge required
Access to a computer with internet
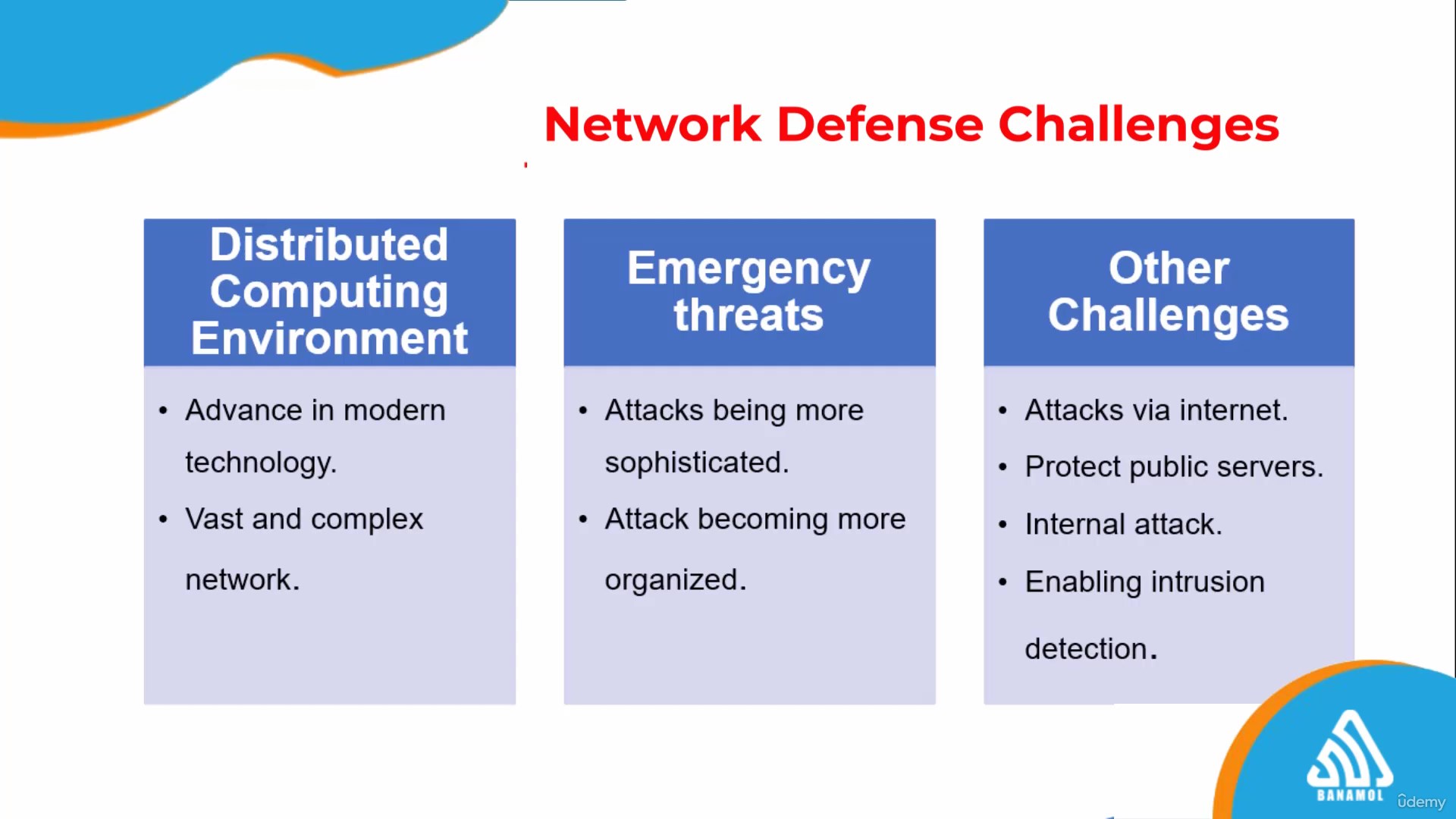
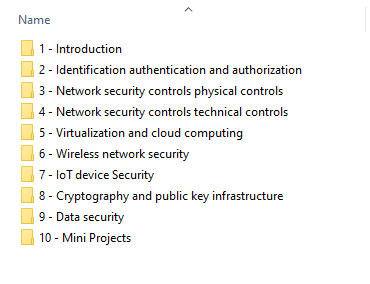
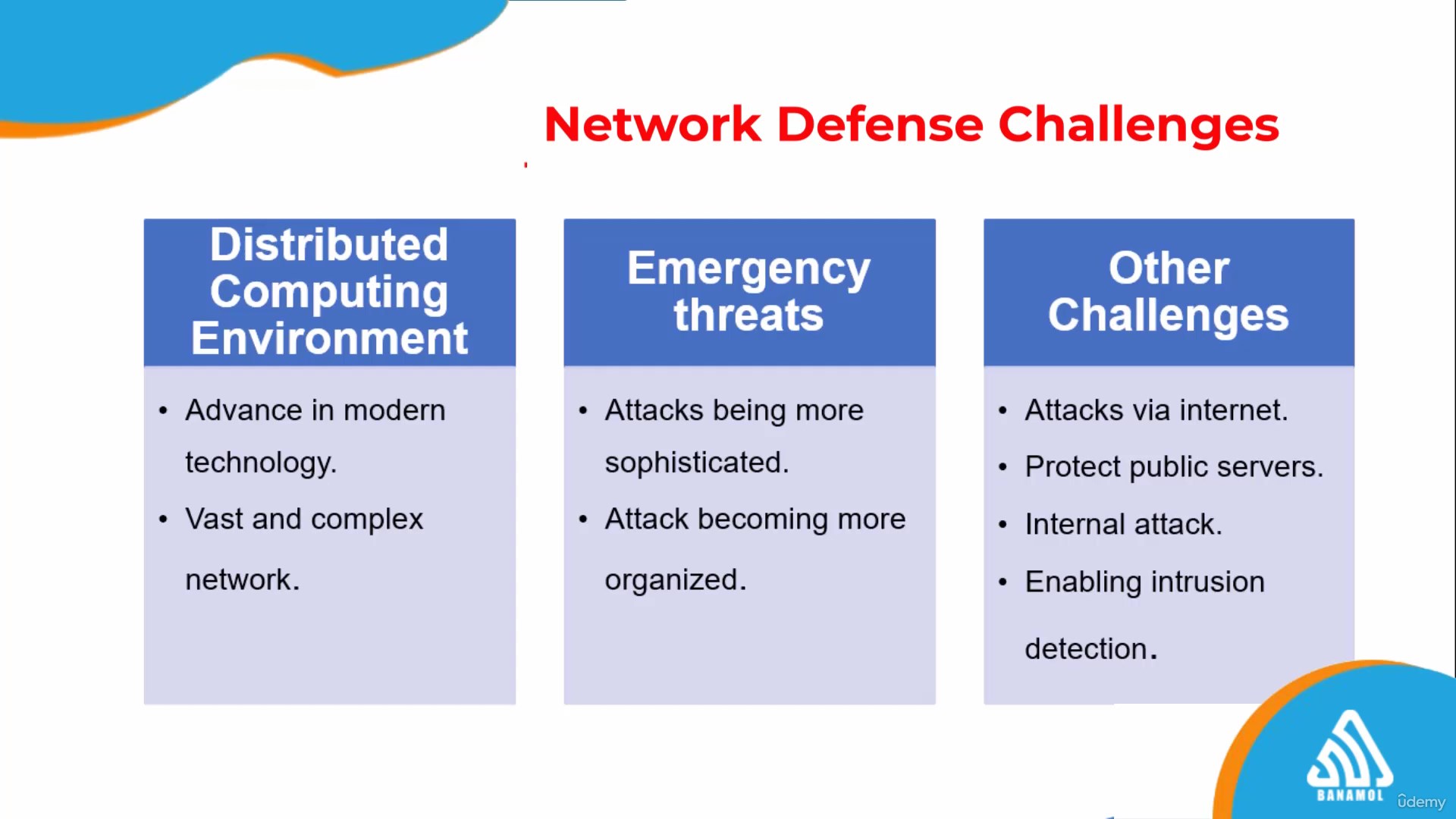
Dive into the realm of network security with our "Network Defense Essentials" course, meticulously designed to equip you with a robust foundation in protecting digital infrastructures. This course will take you through a detailed exploration of network defense strategies, starting with an introduction to essential concepts such as network security controls, basic Linux operations, and the various types of defense mechanisms available.
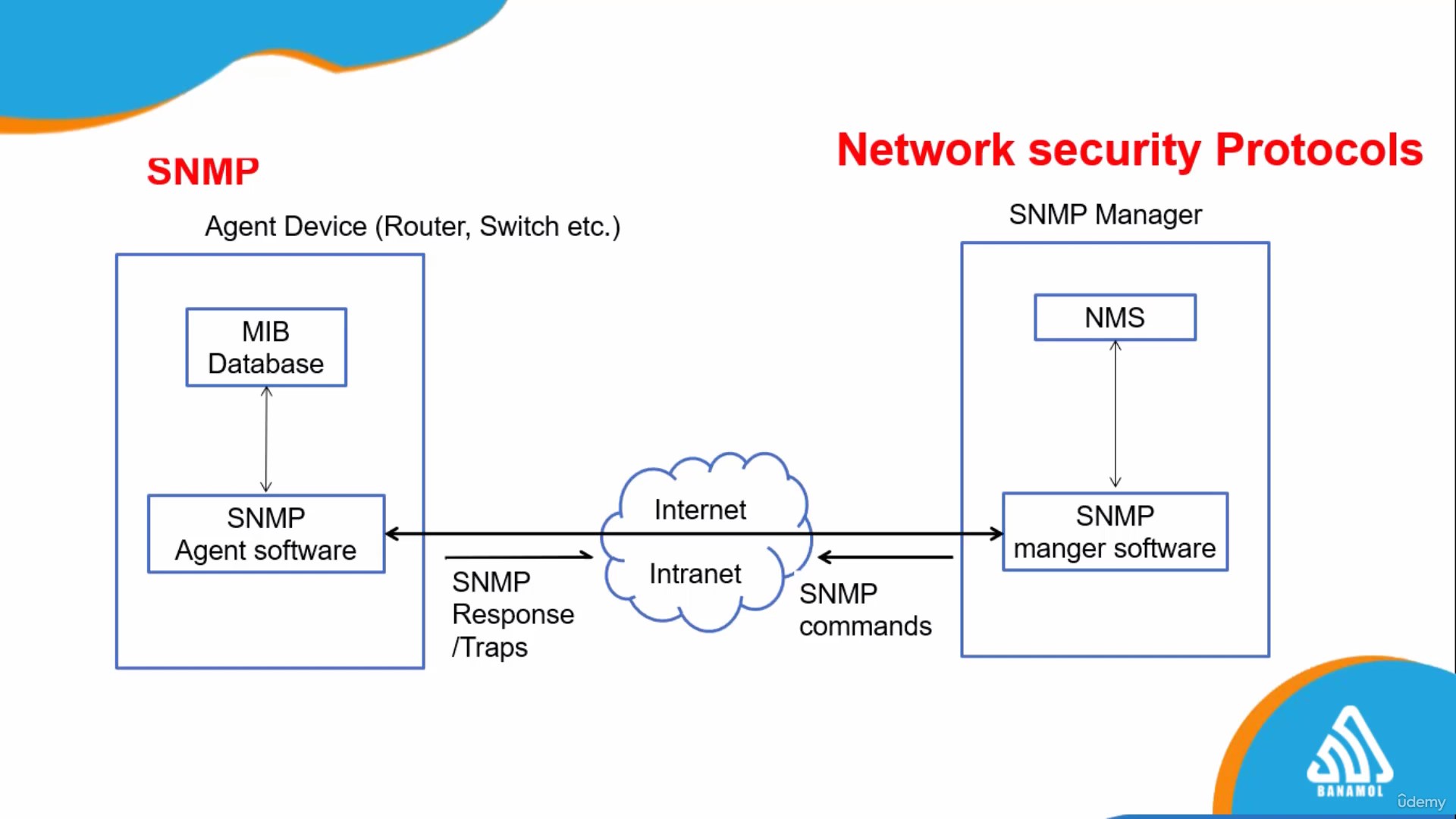
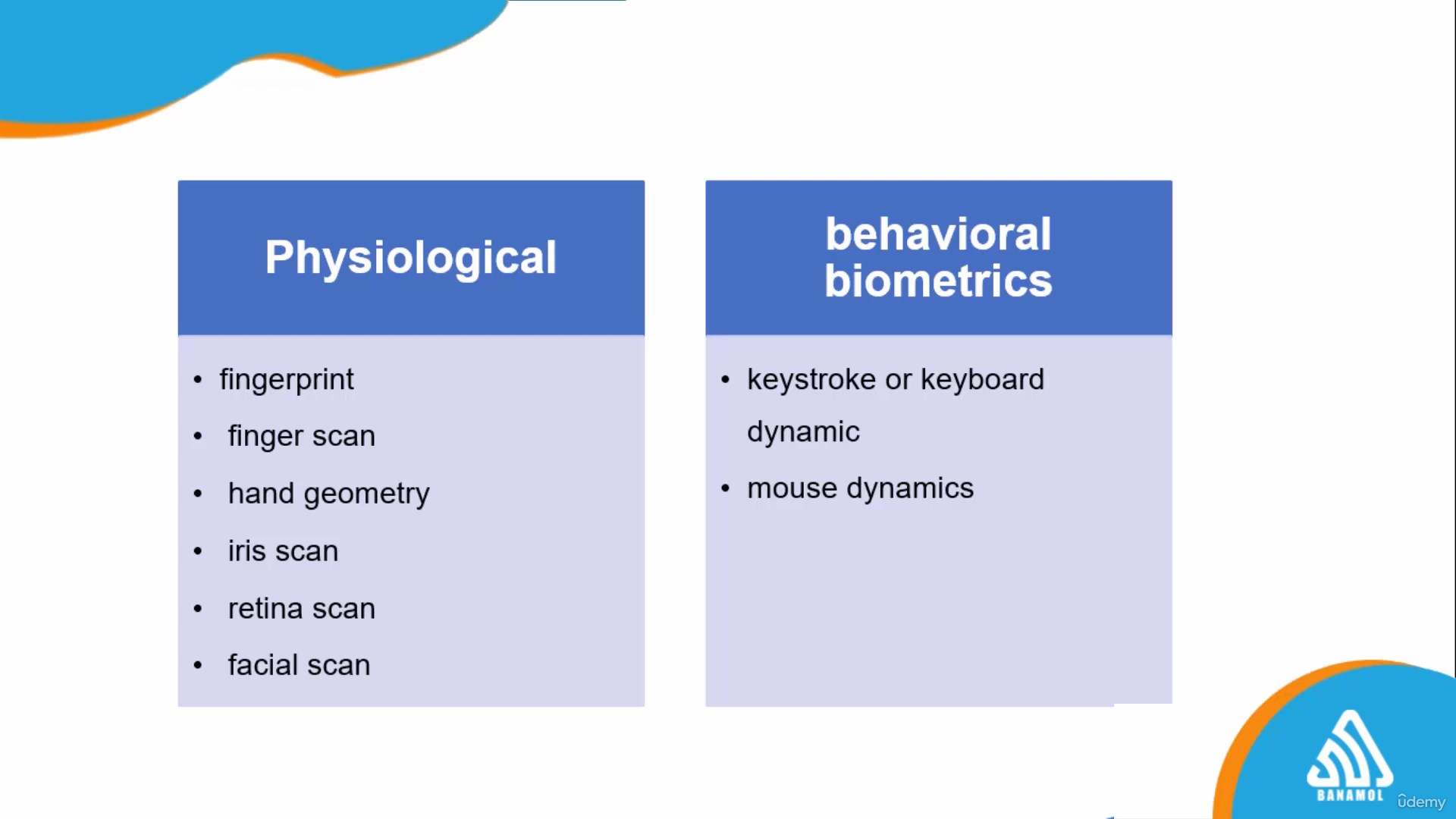
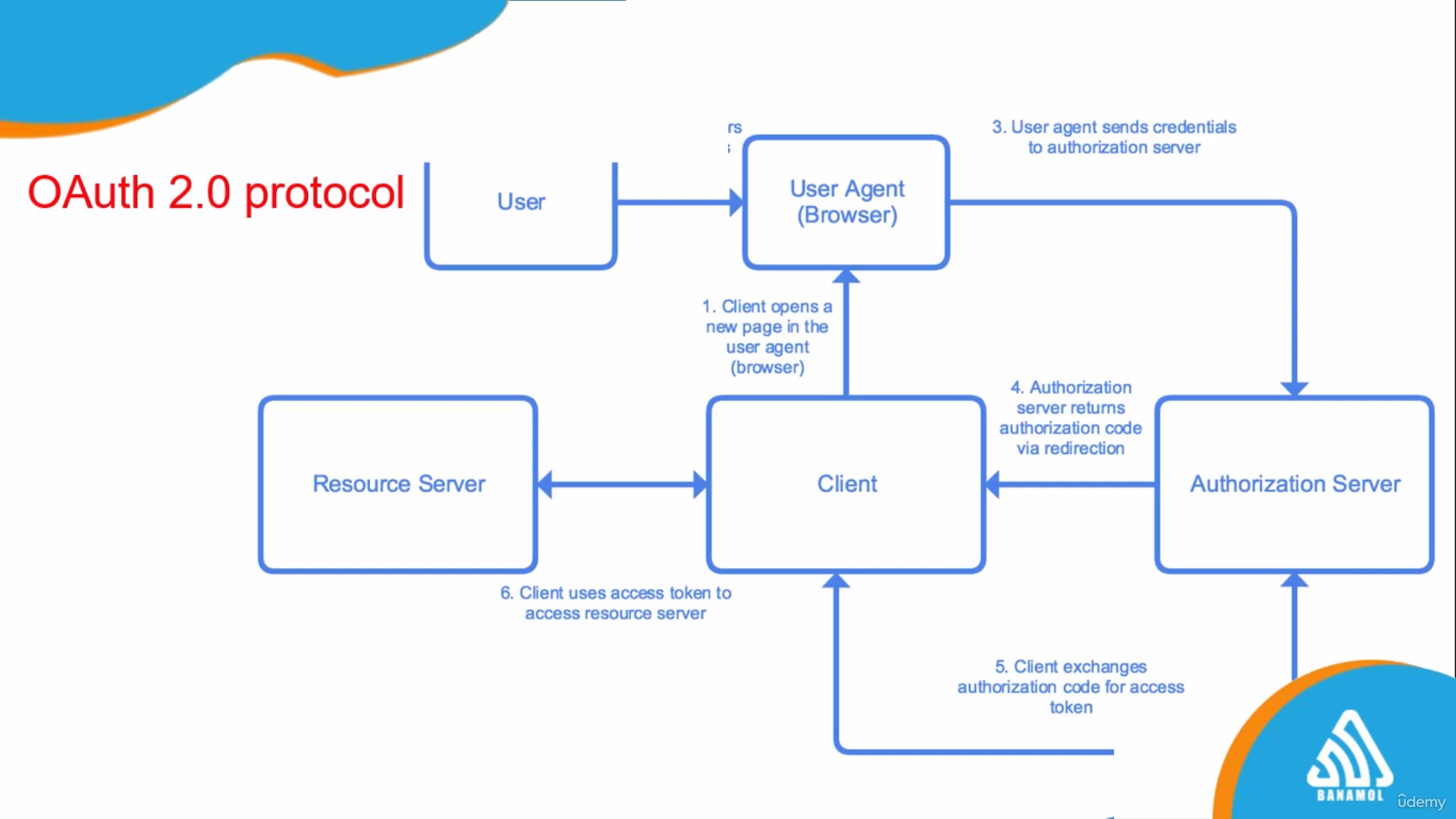
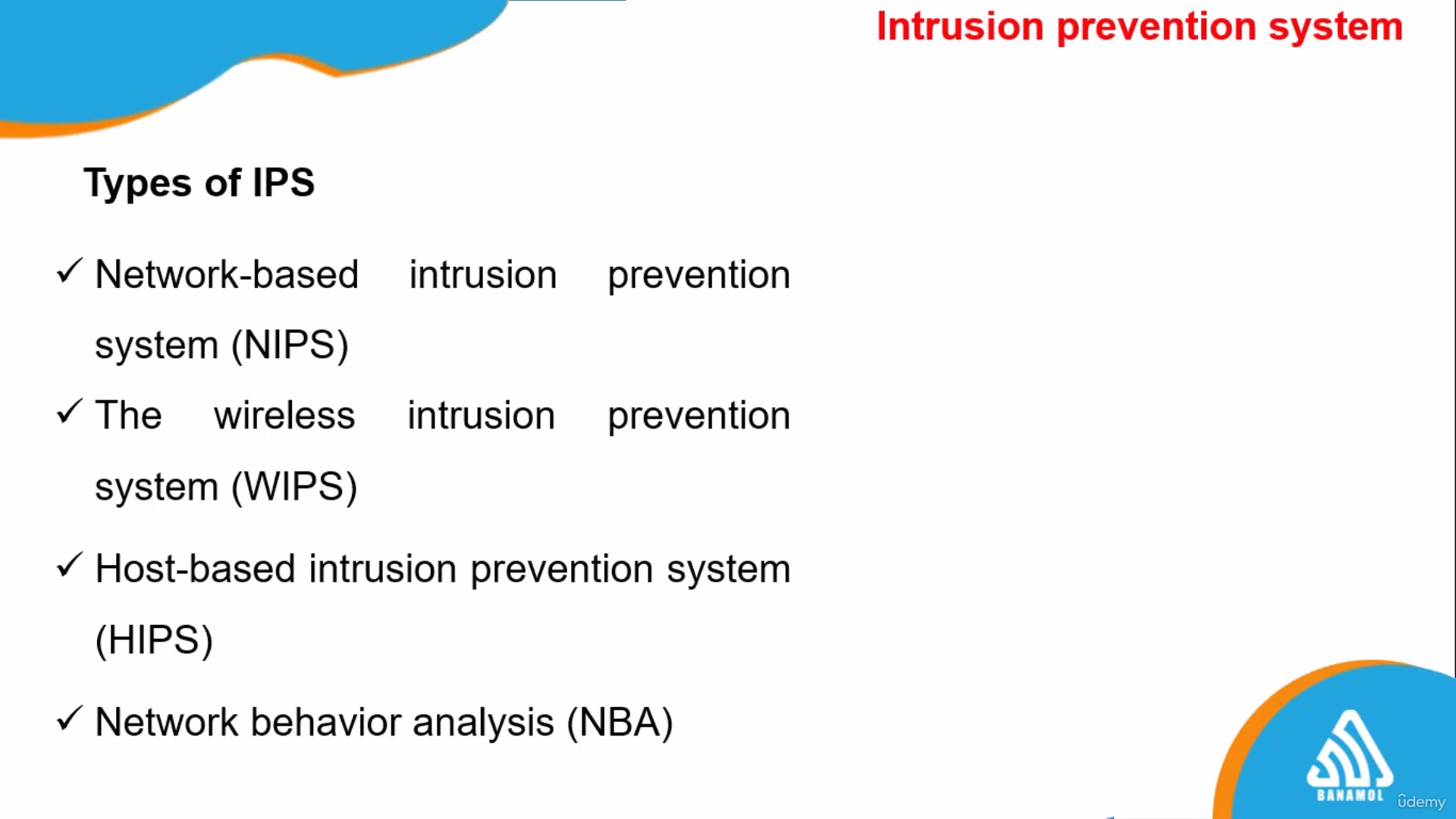
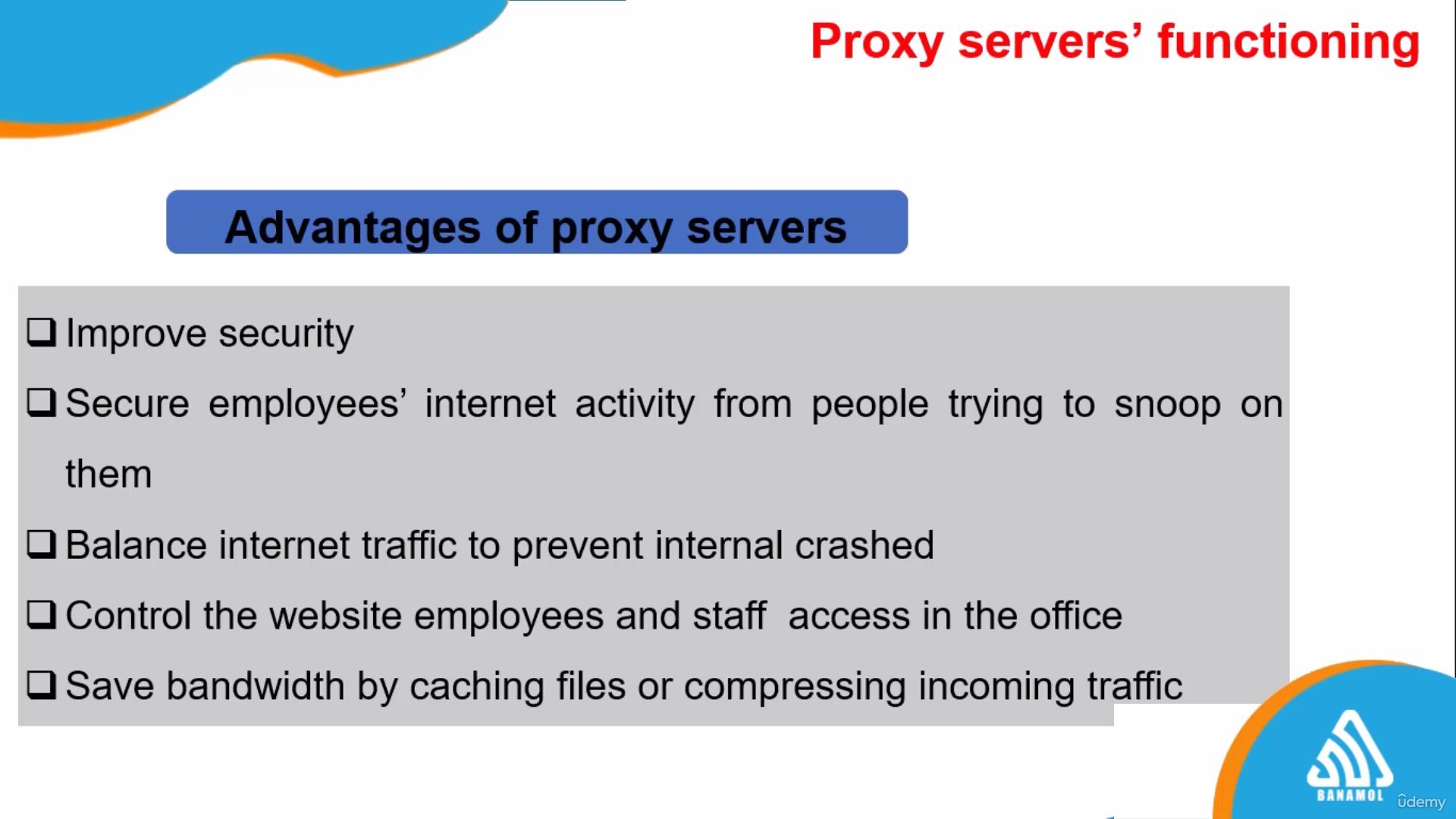
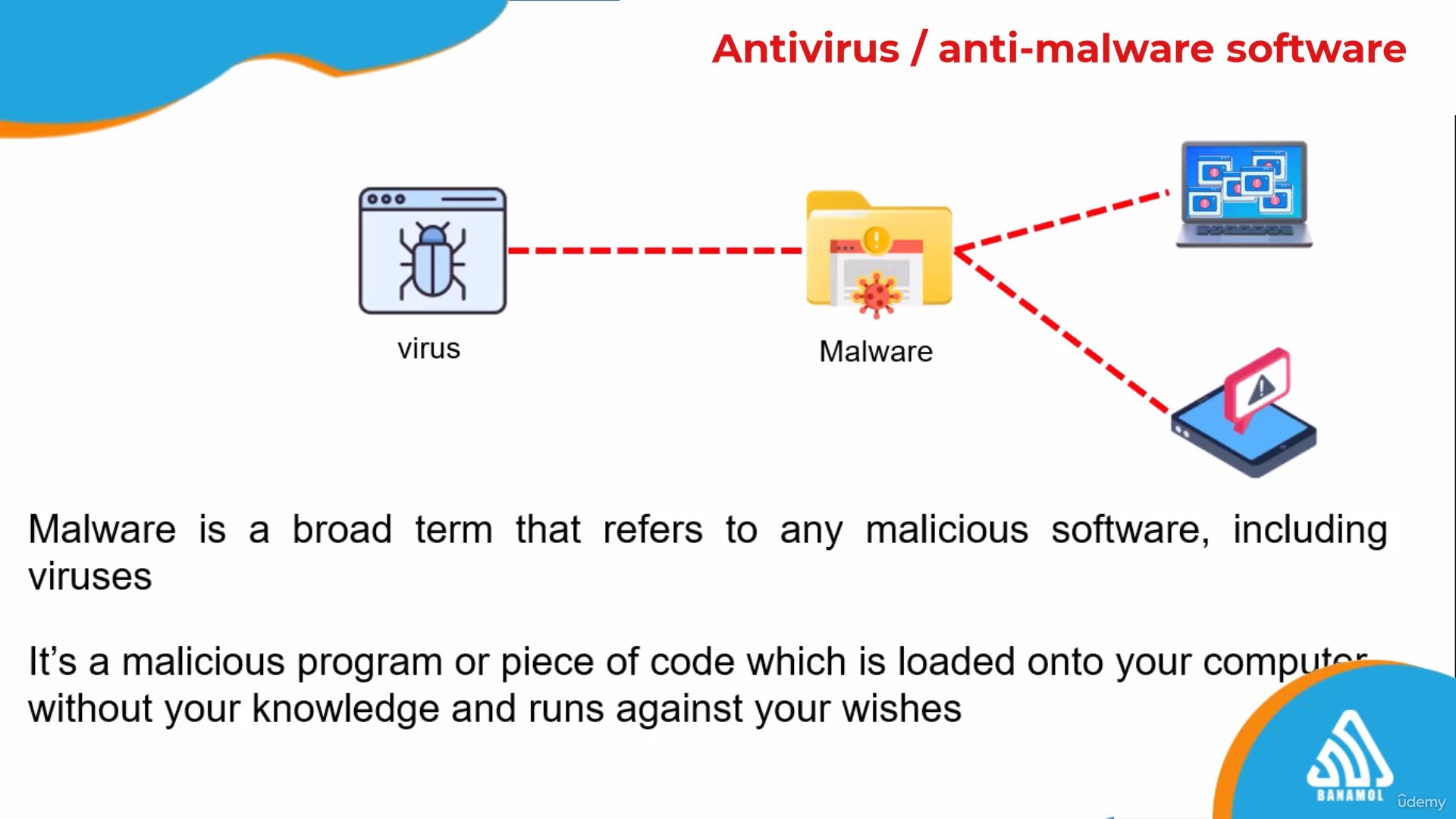
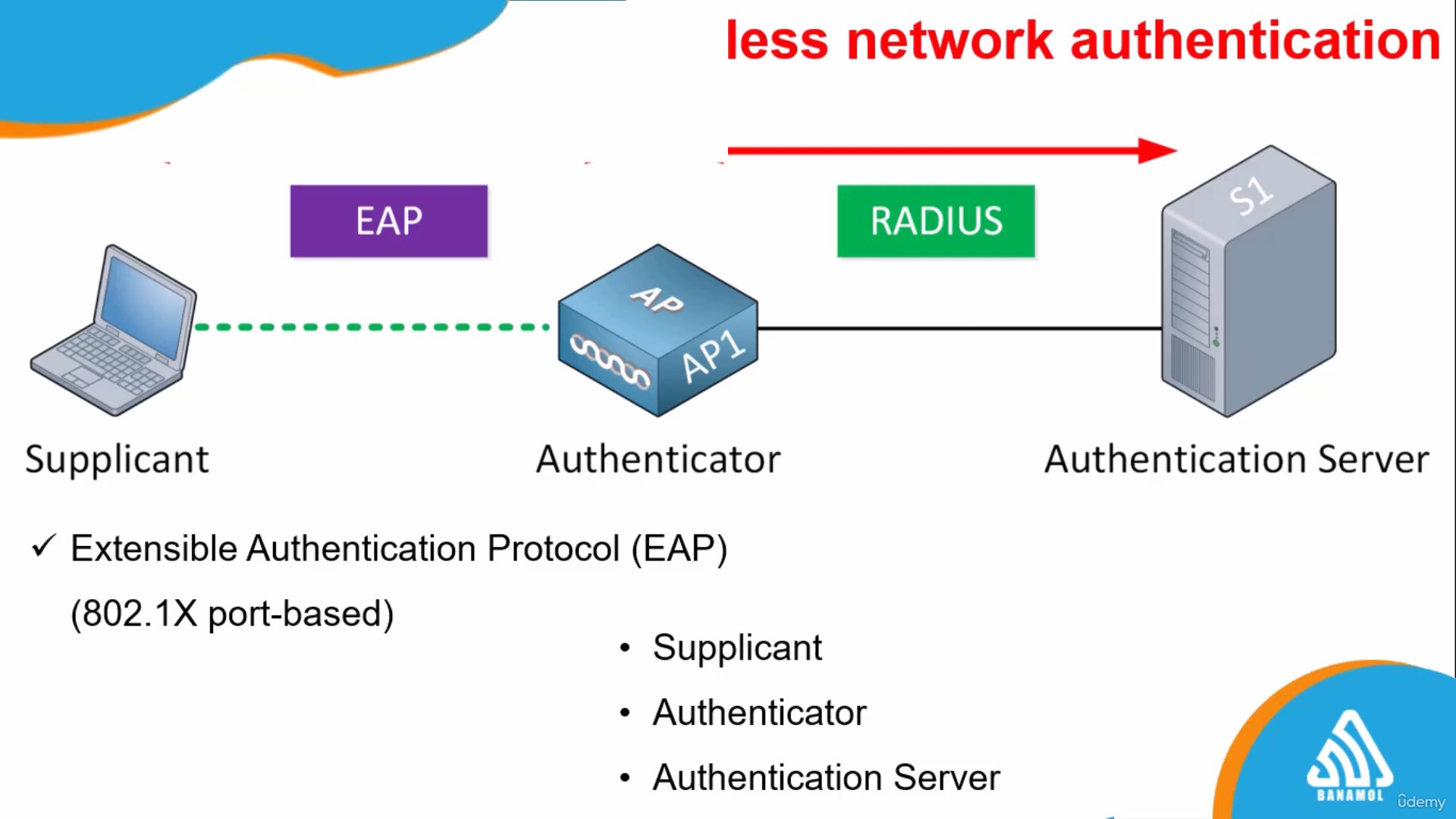
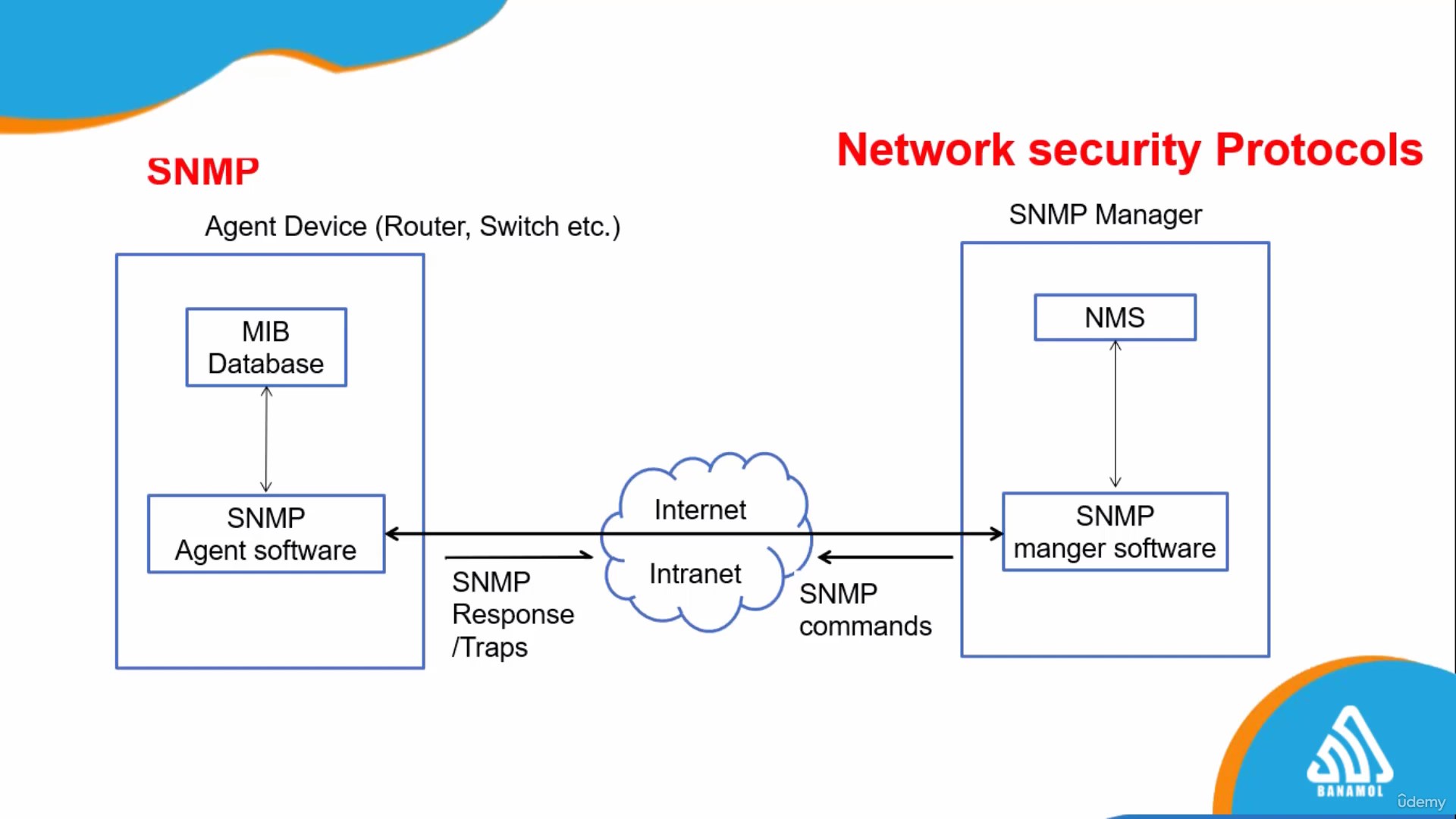
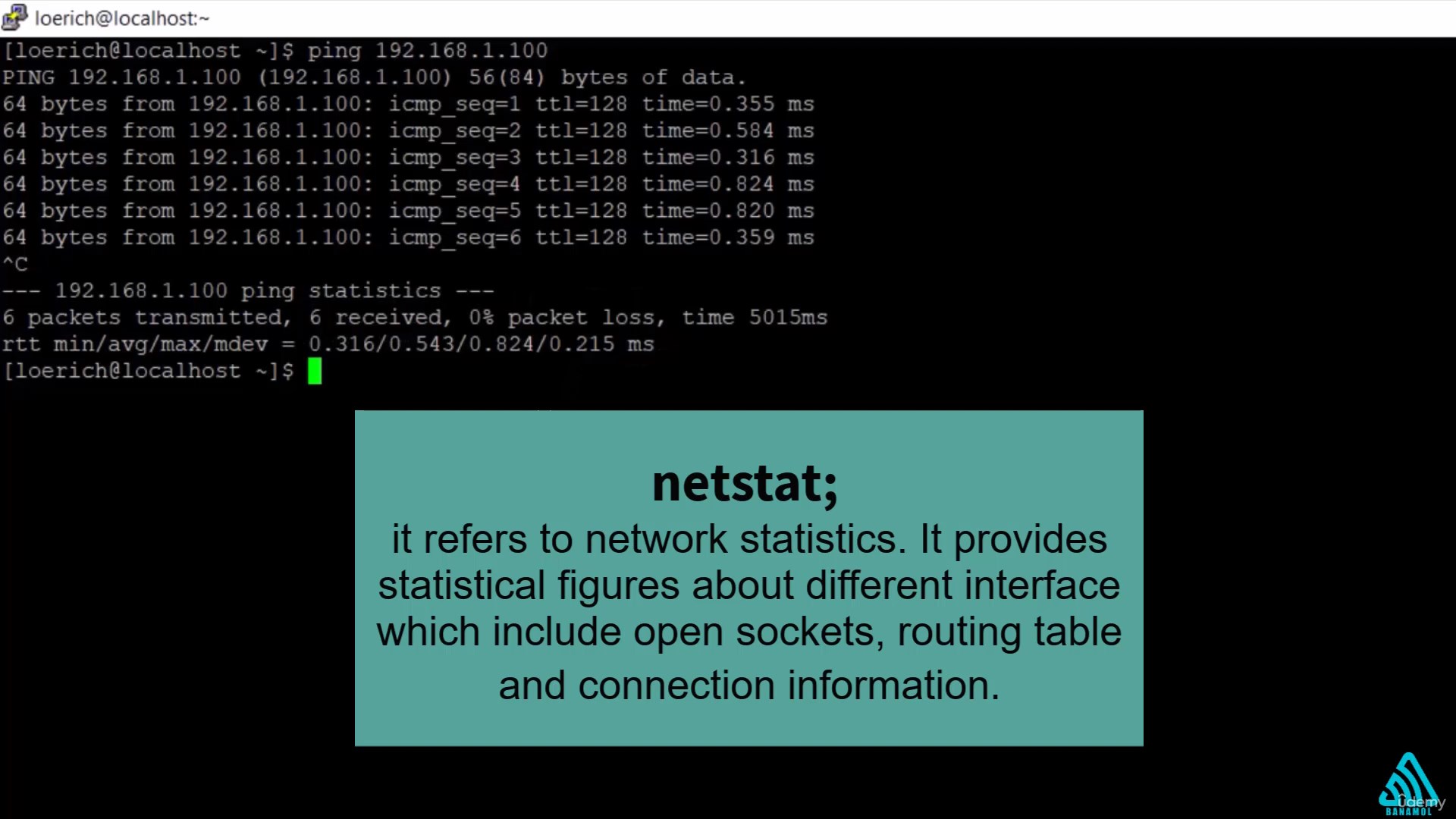
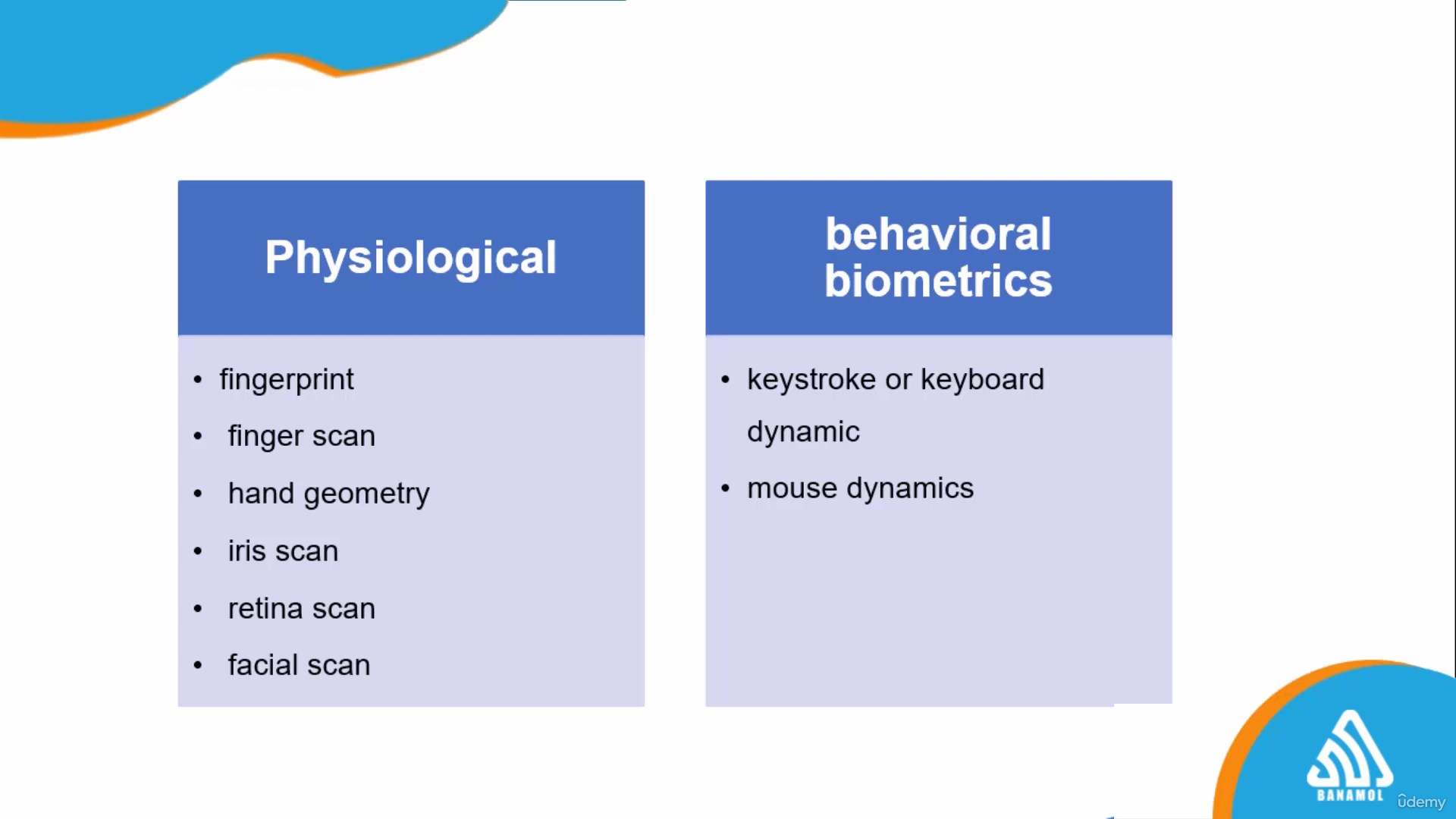
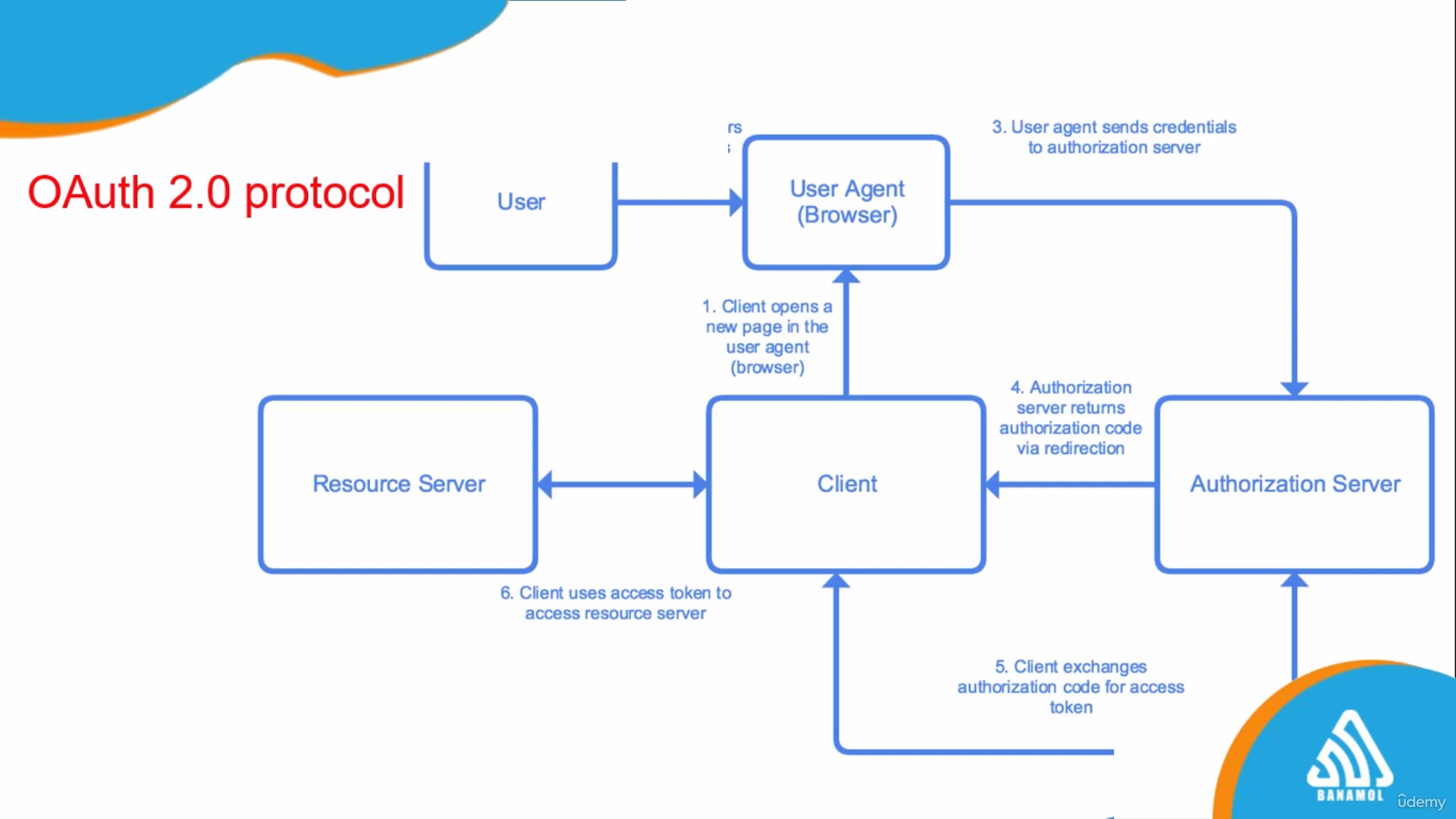
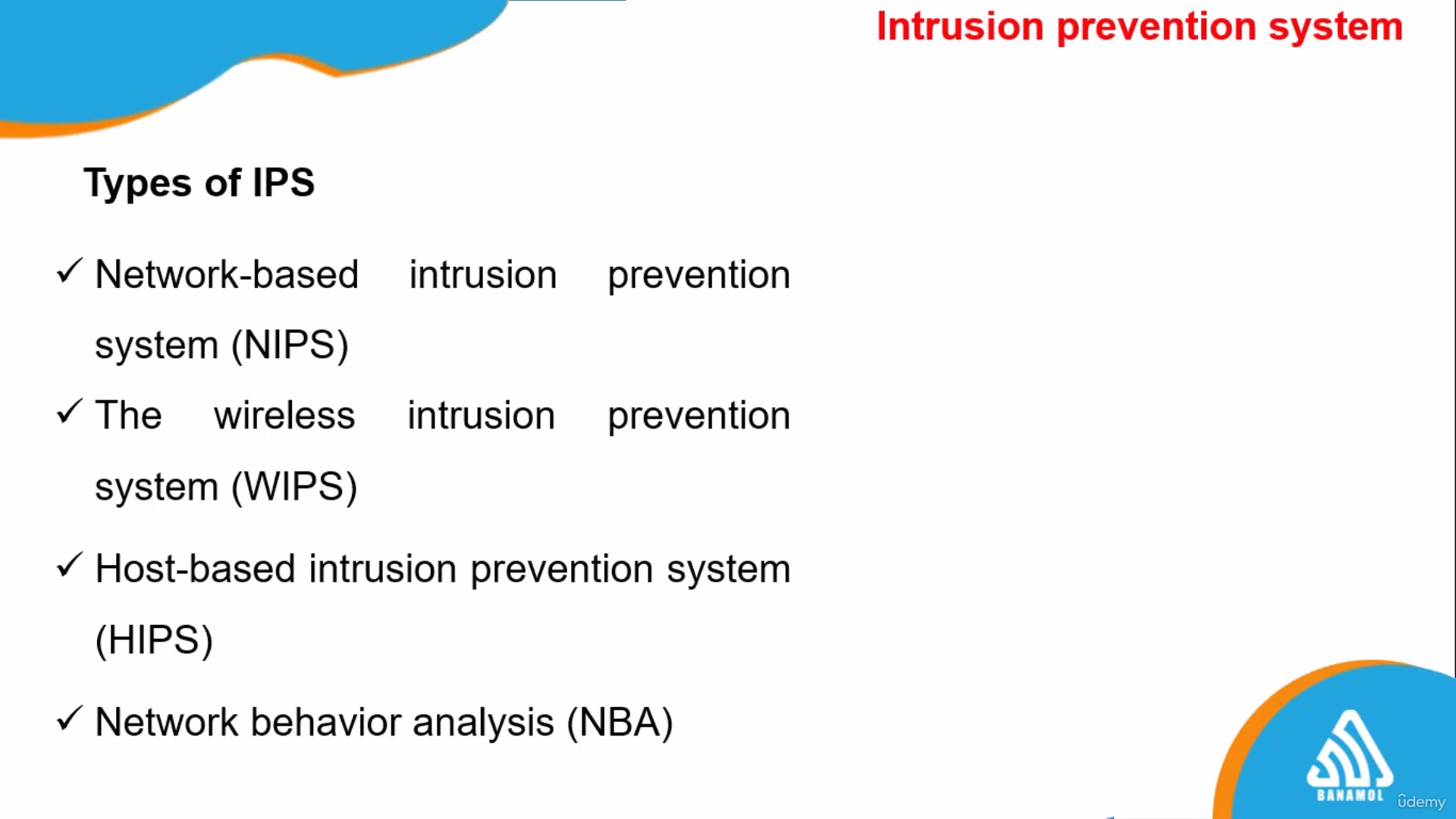
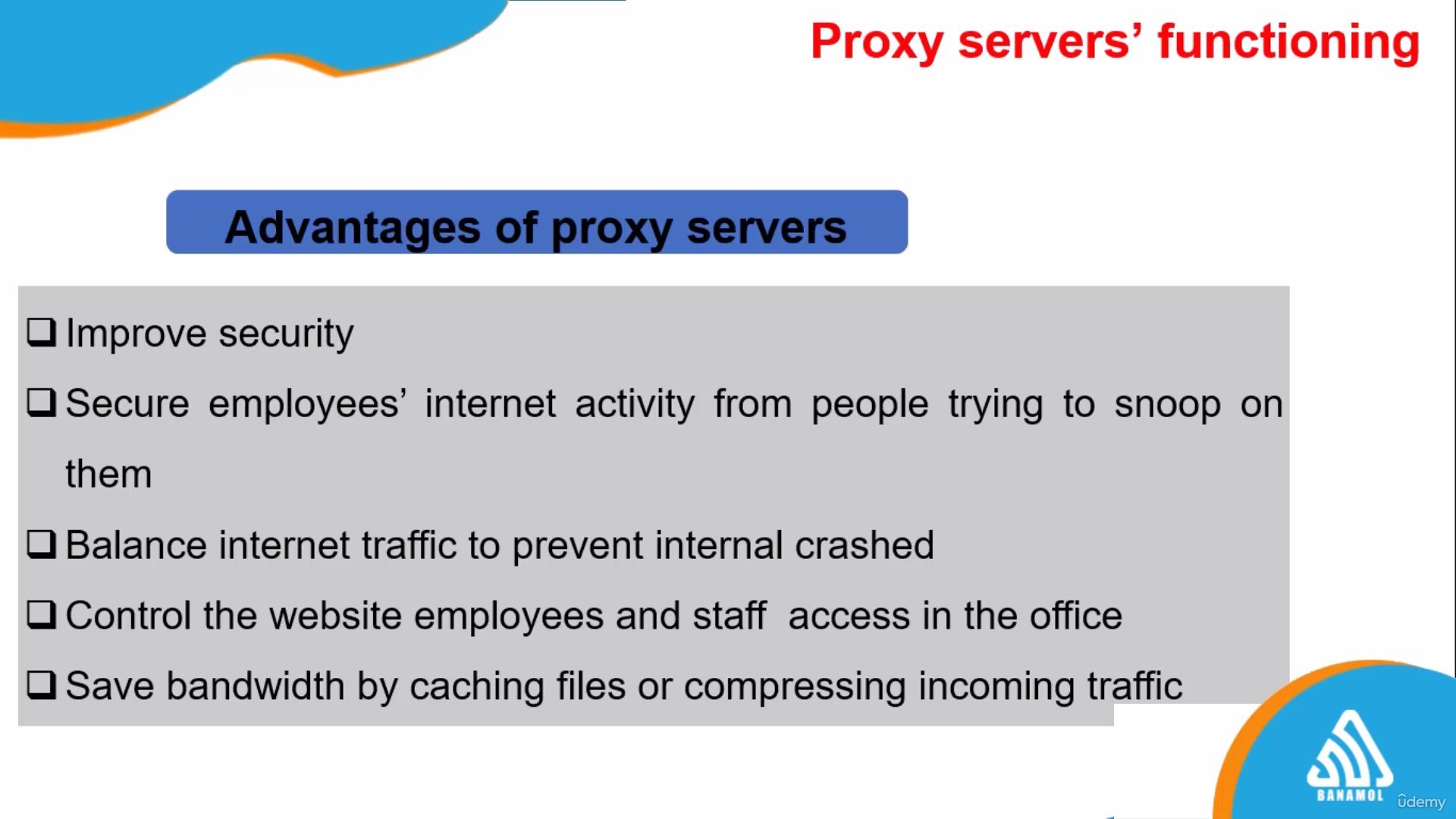
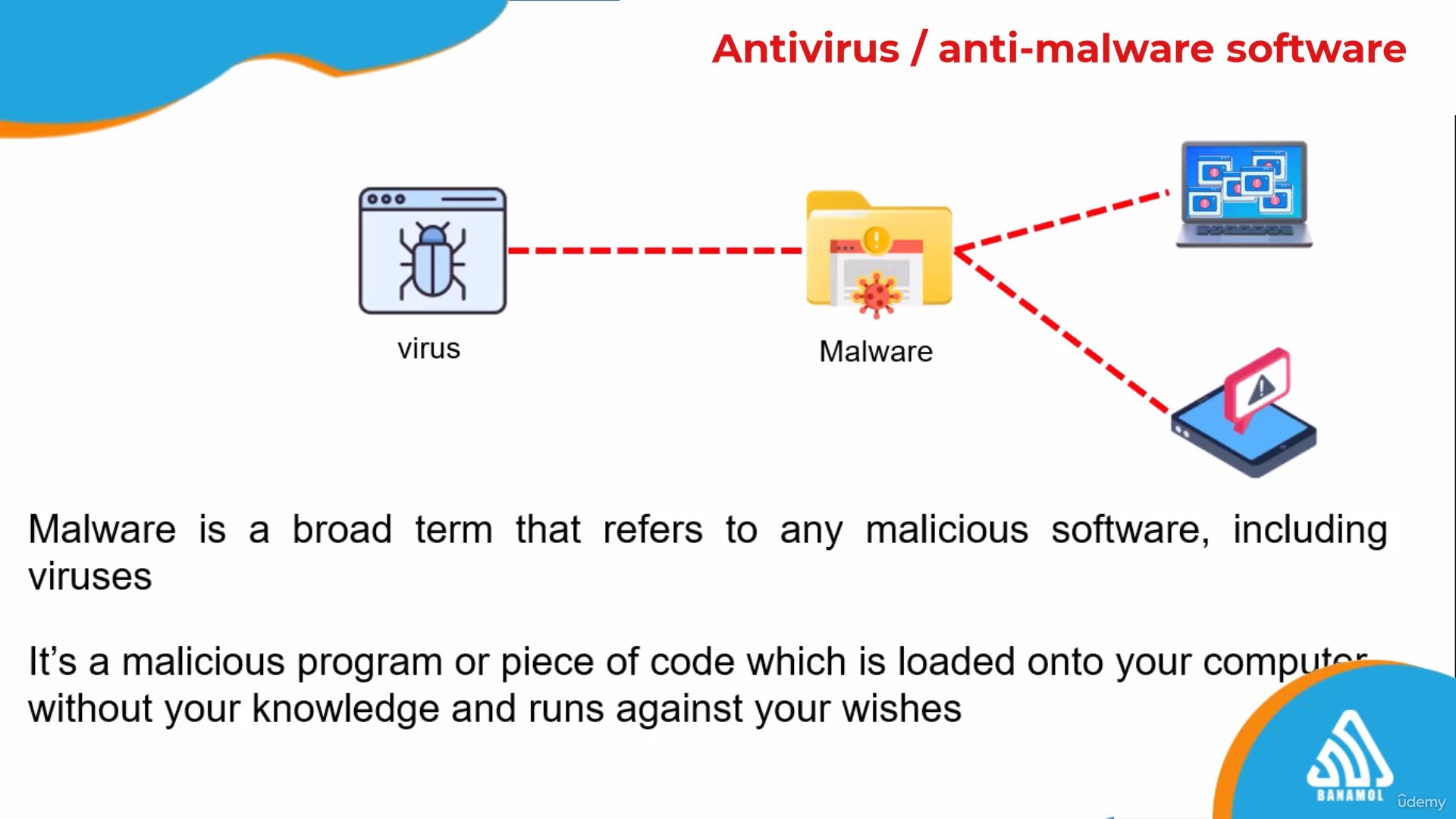
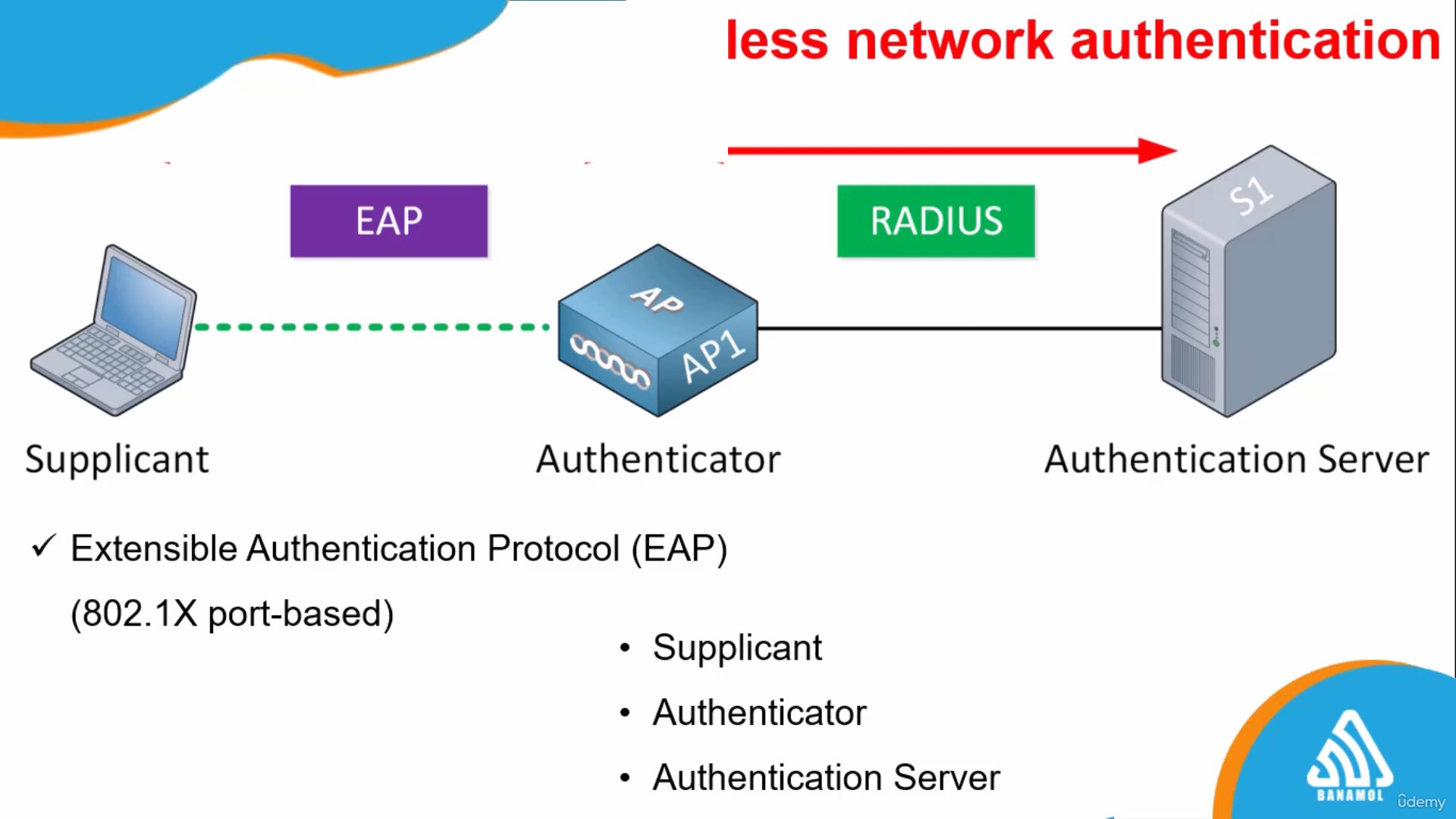
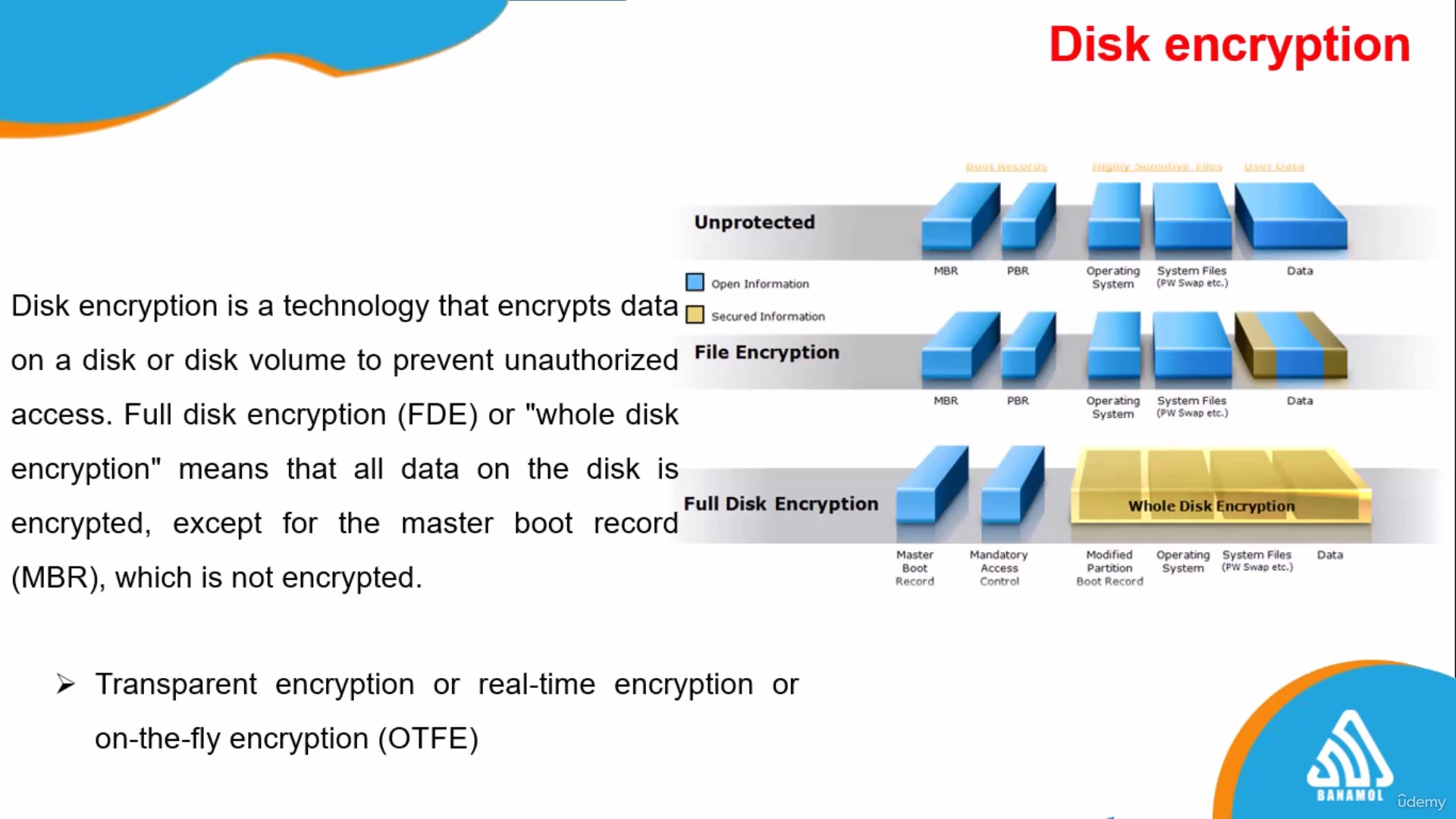
Over the span of several focused sessions, you will delve into critical areas including identification processes, authentication methods, and authorization procedures. Learn about physical security controls to combat potential attack vectors, and gain in-depth knowledge of technical controls such as firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), proxy servers, and the crucial roles they play in network segmentation.
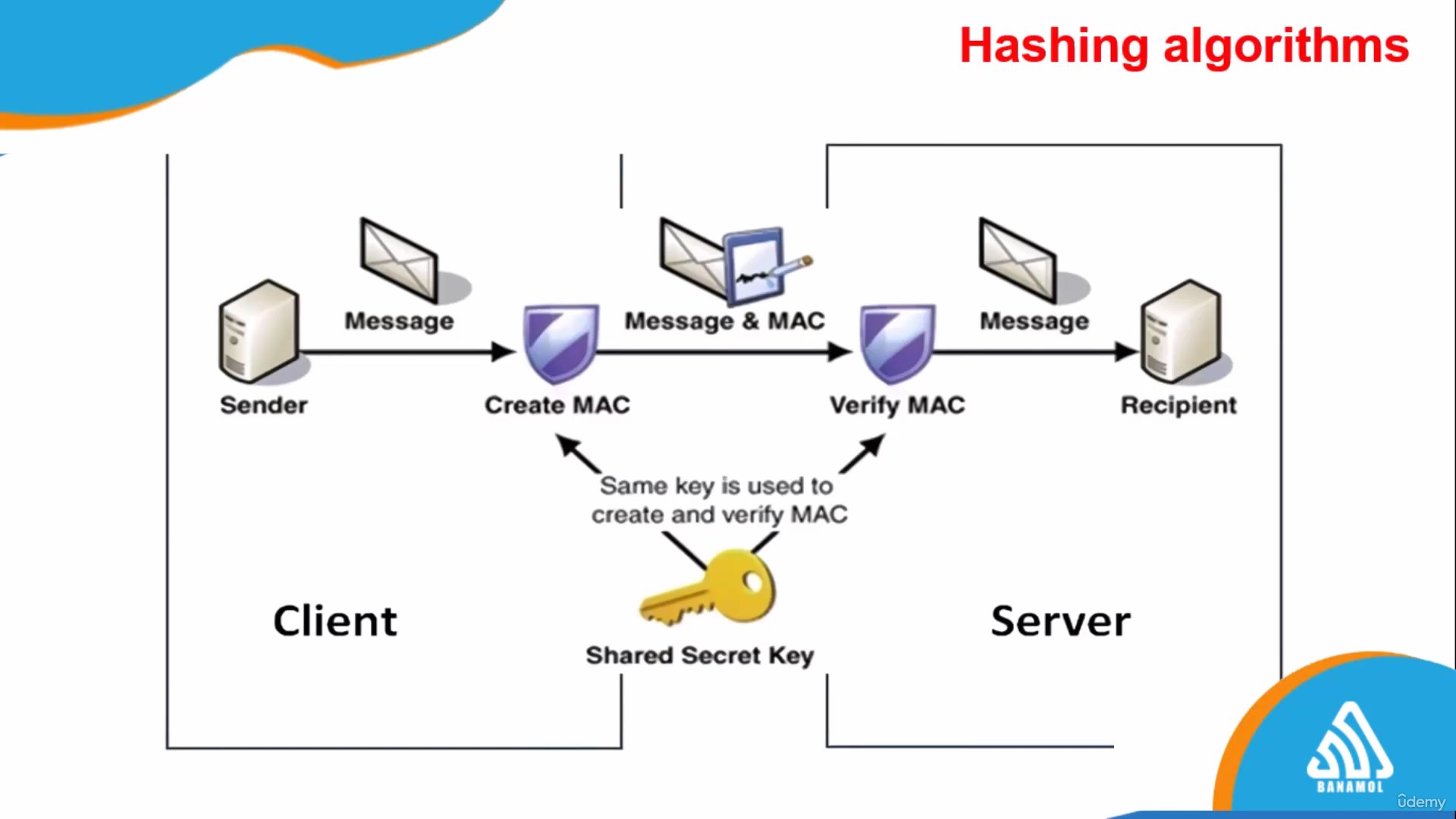
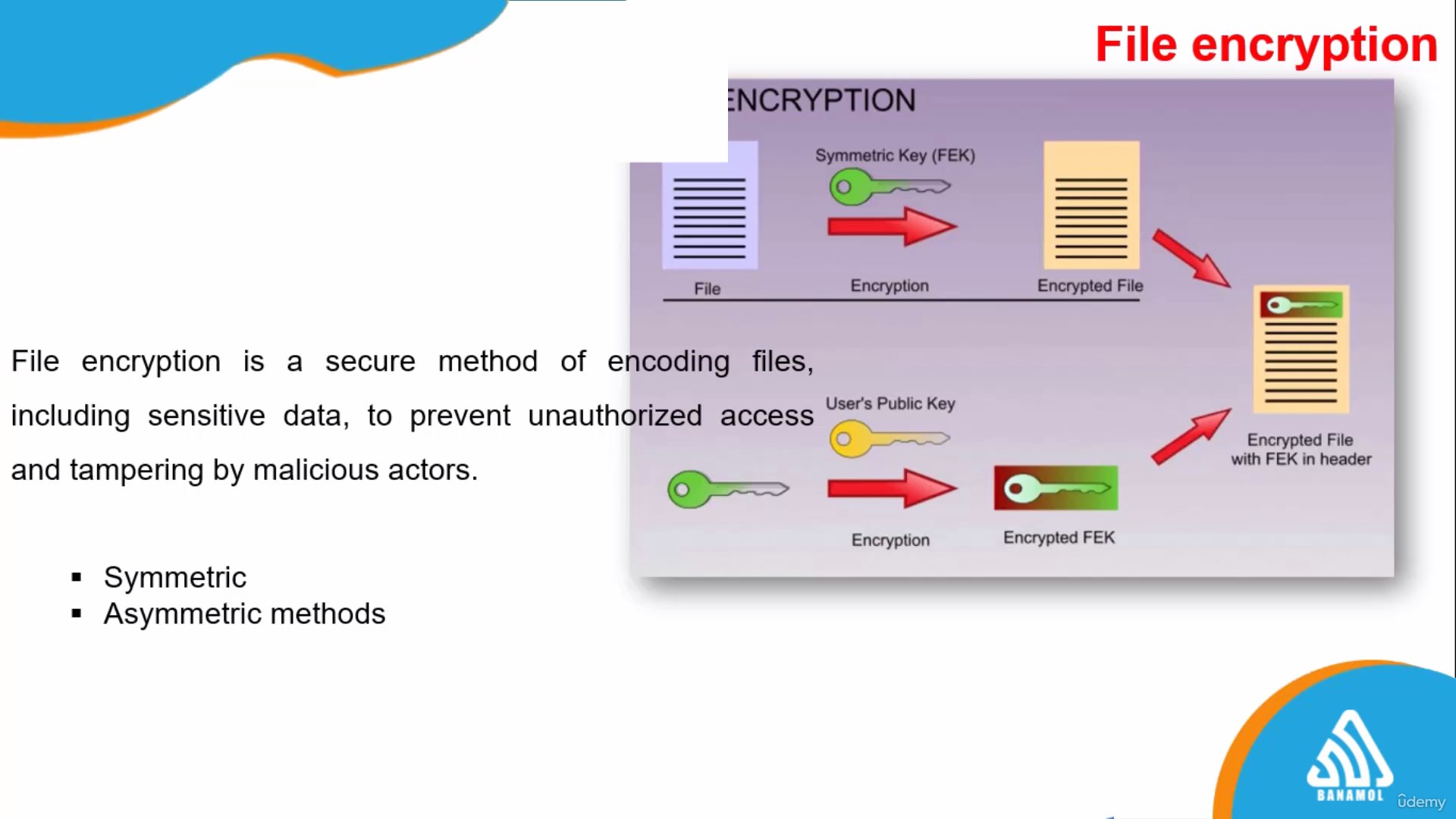
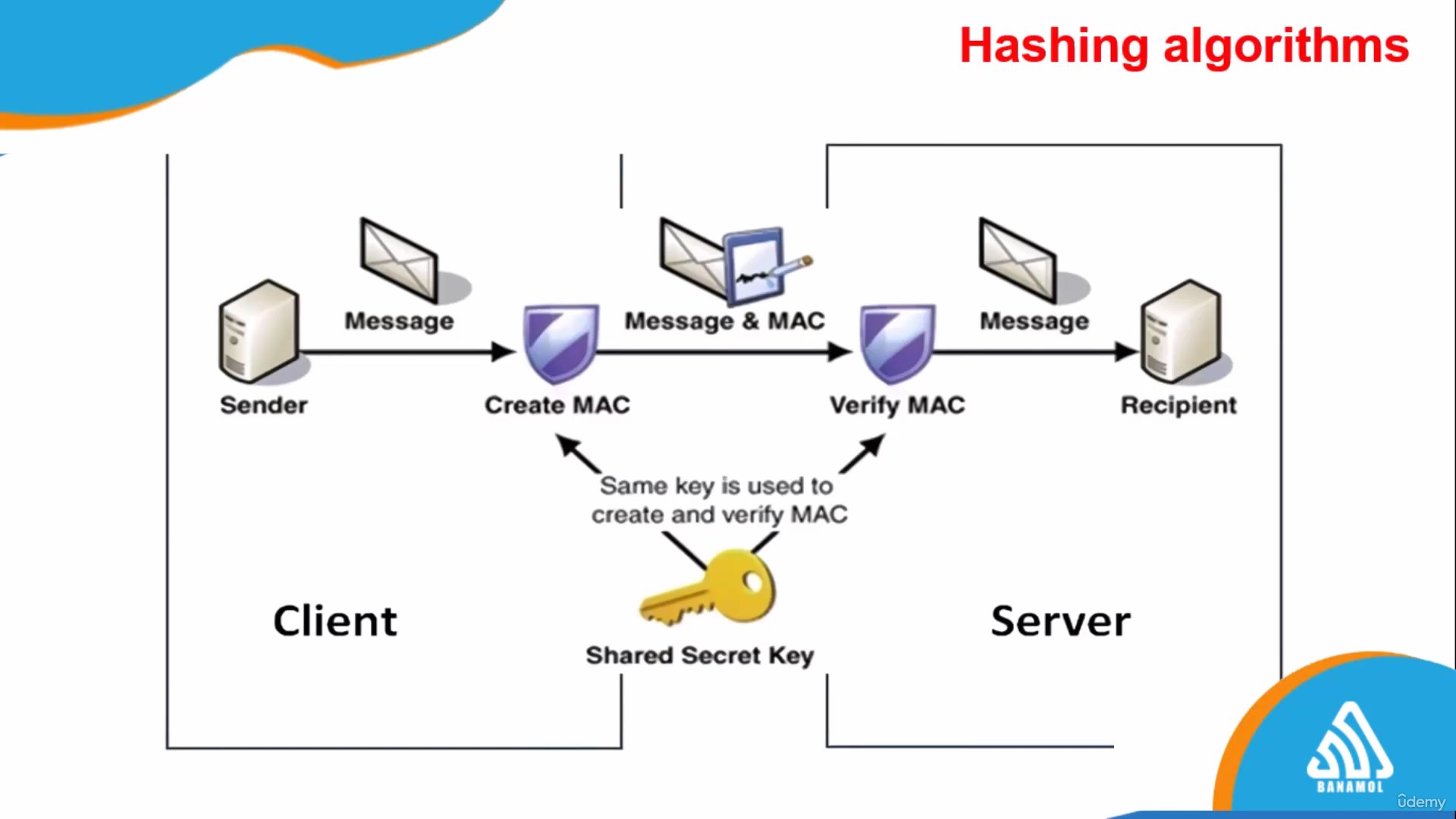
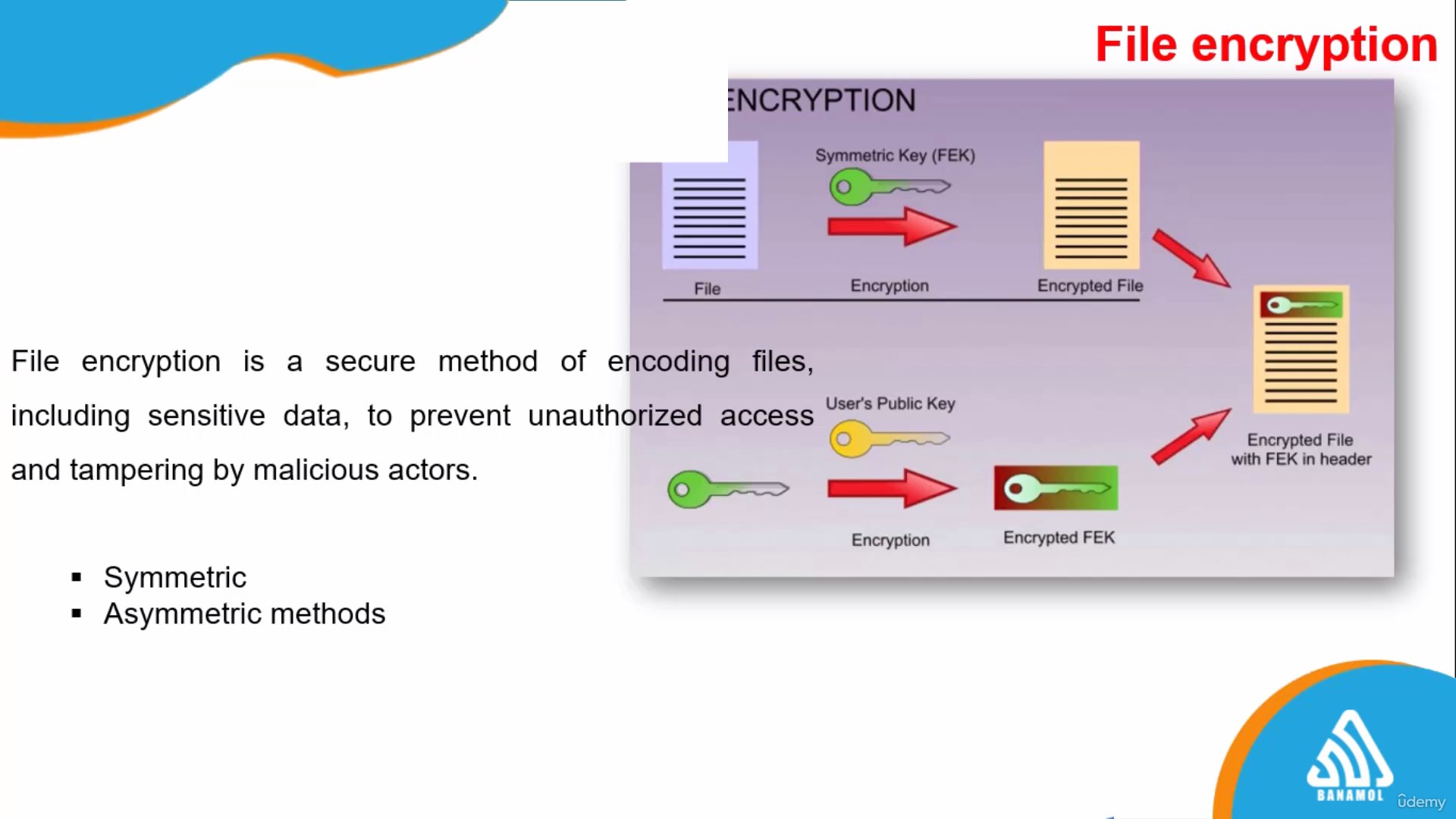
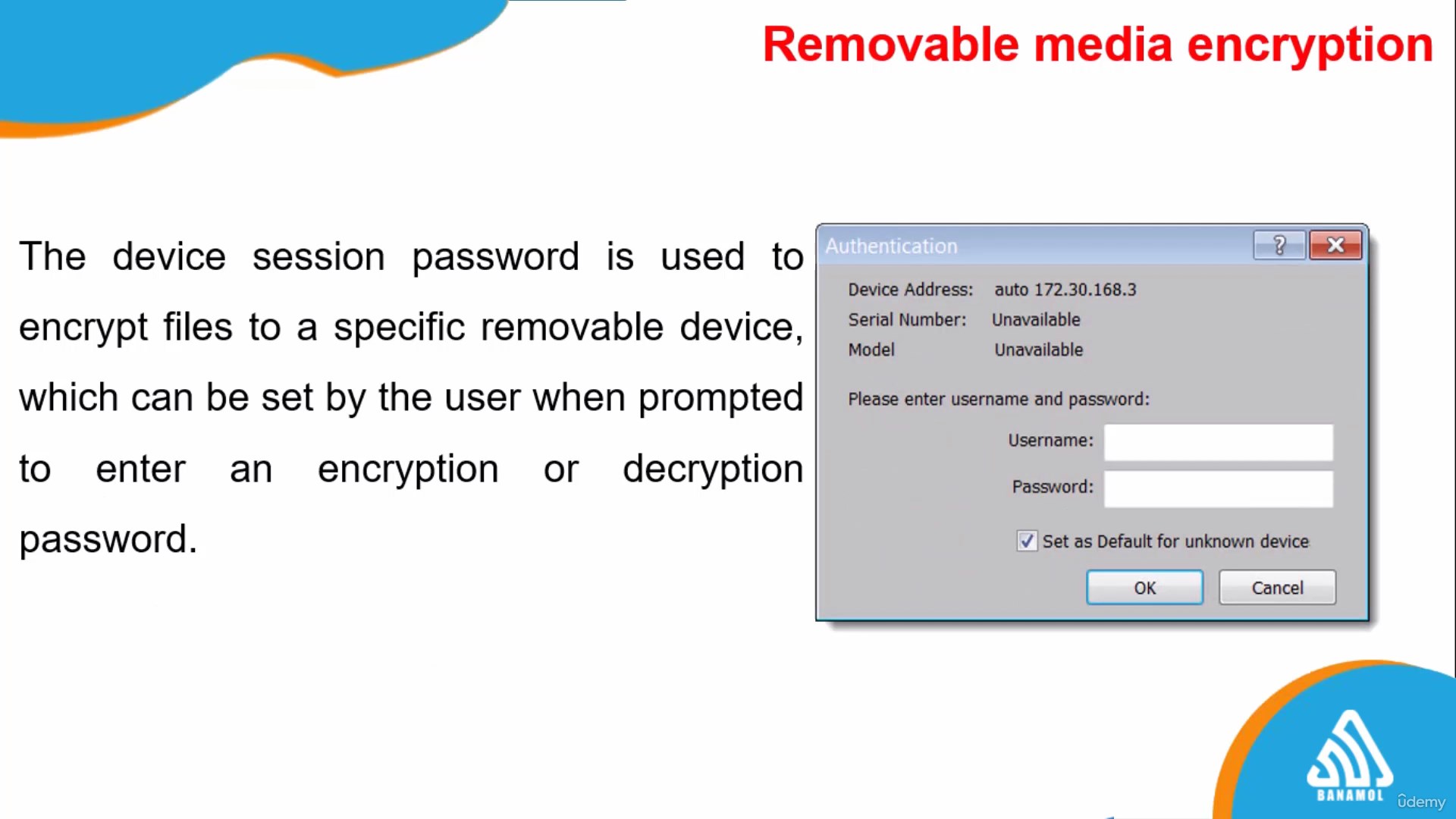
Further enhancing your expertise, the course covers virtualization and cloud computing security, highlighting the benefits and best practices of cloud services. You will also navigate through the complexities of wireless network security, IoT device protection, and the pivotal elements of cryptography and public key infrastructure (PKI).
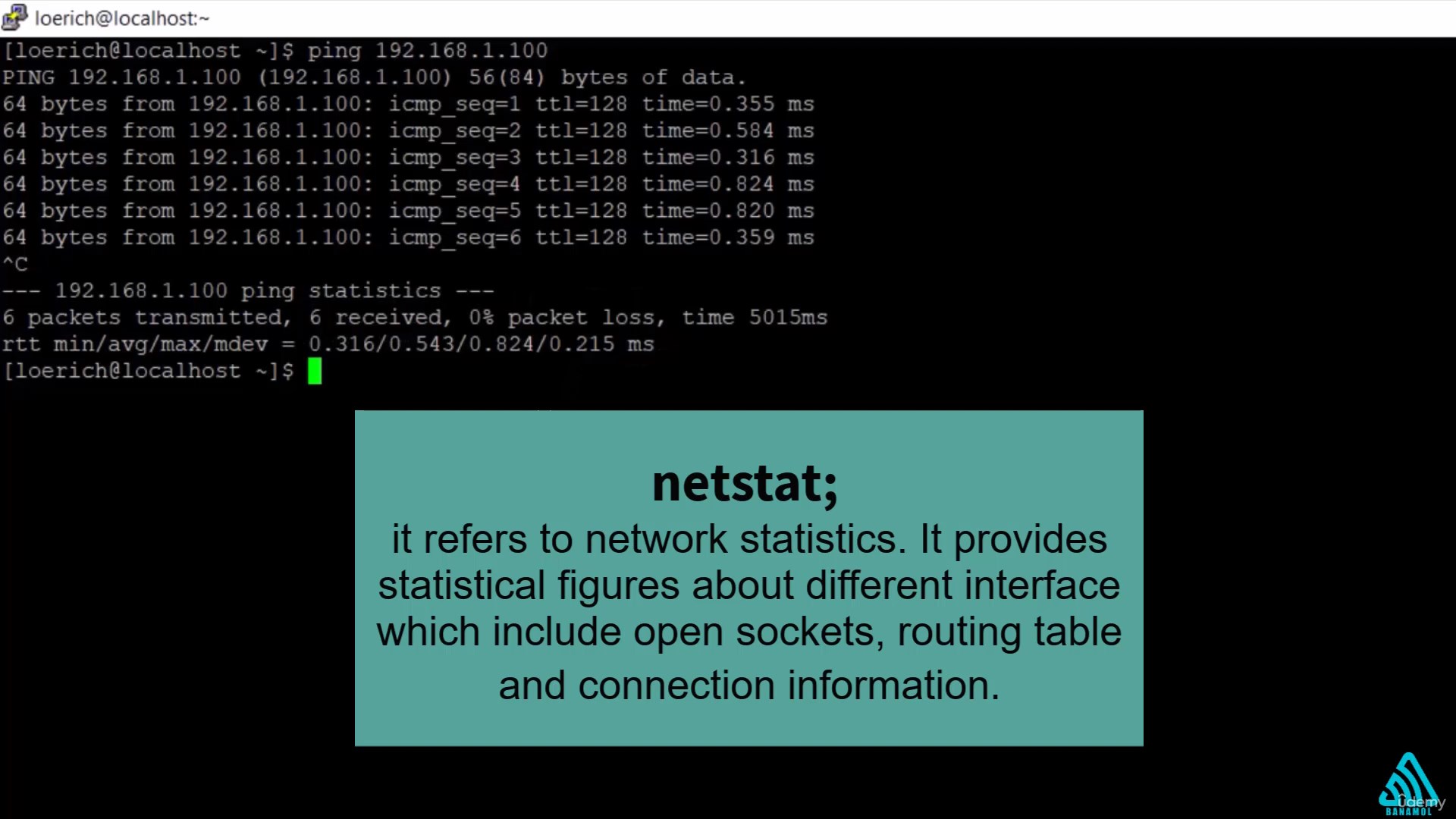
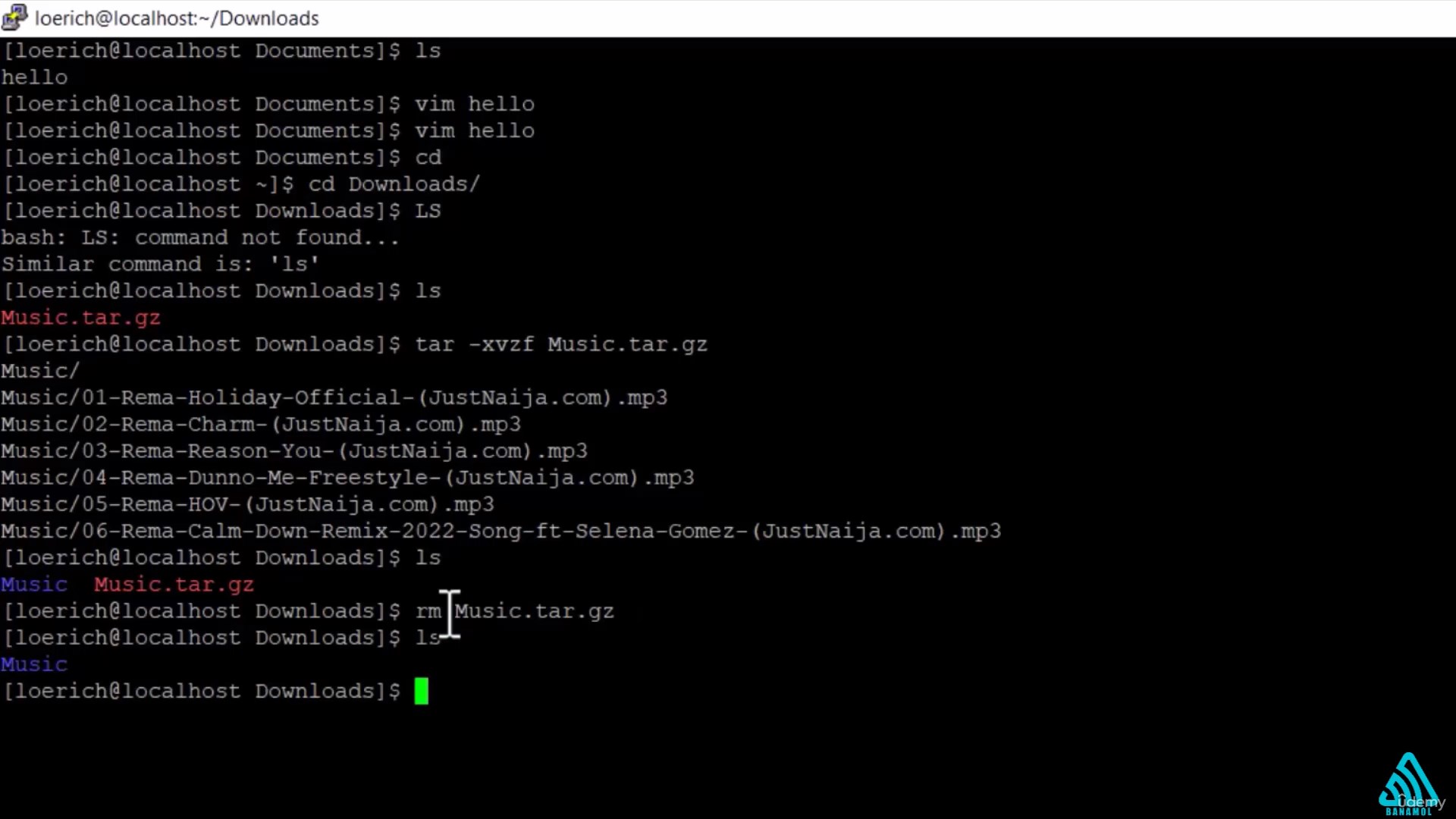
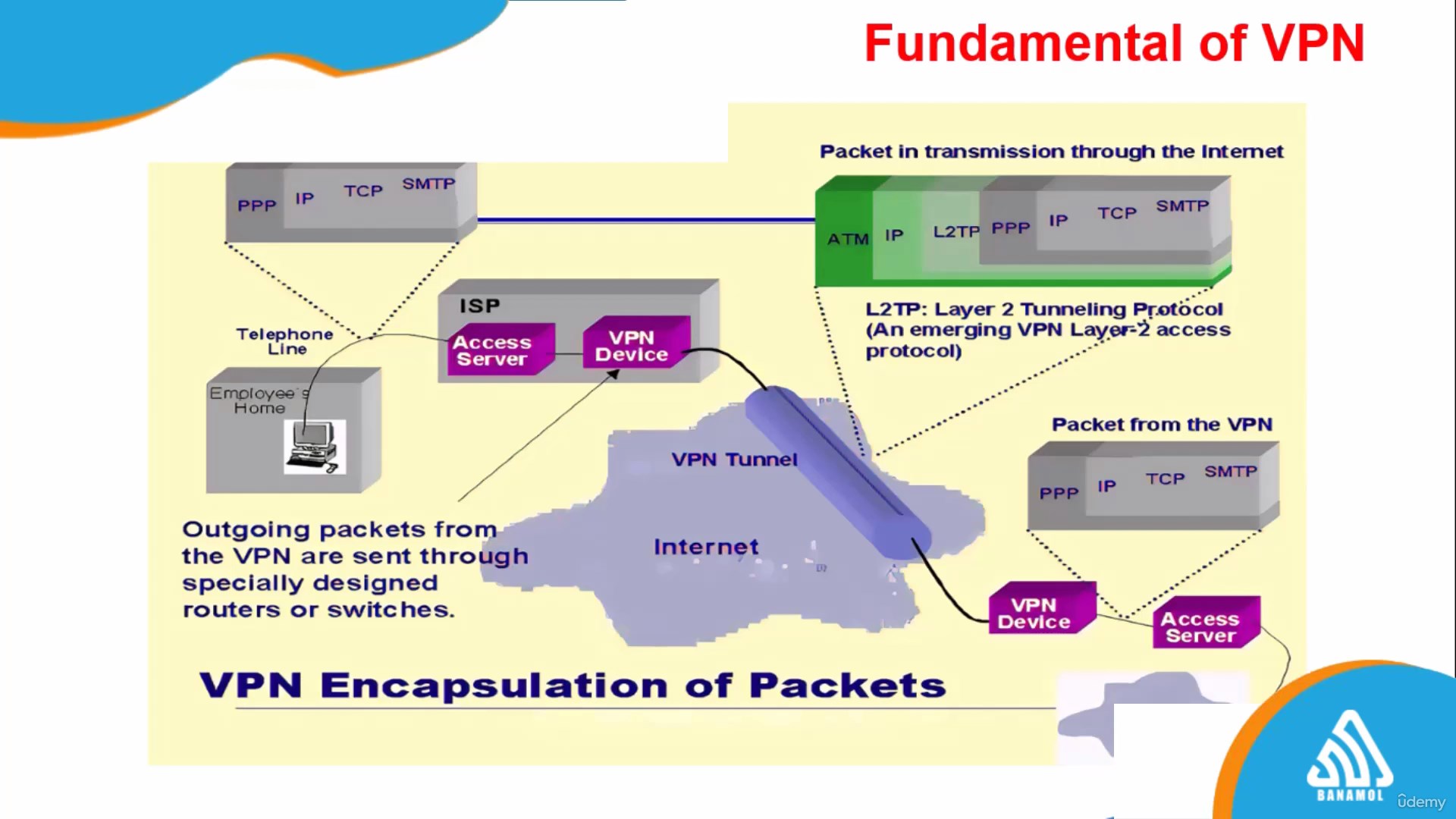
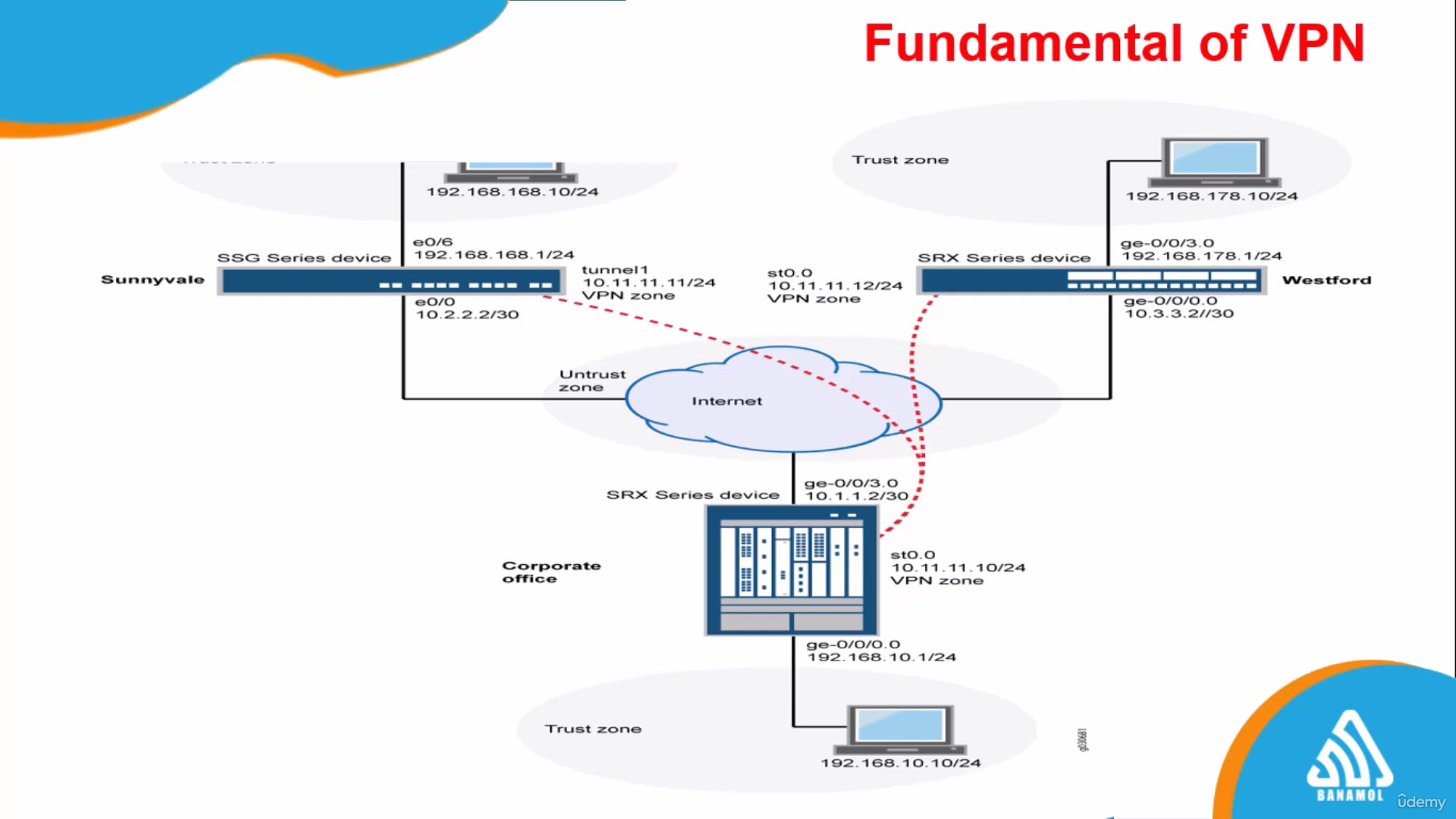
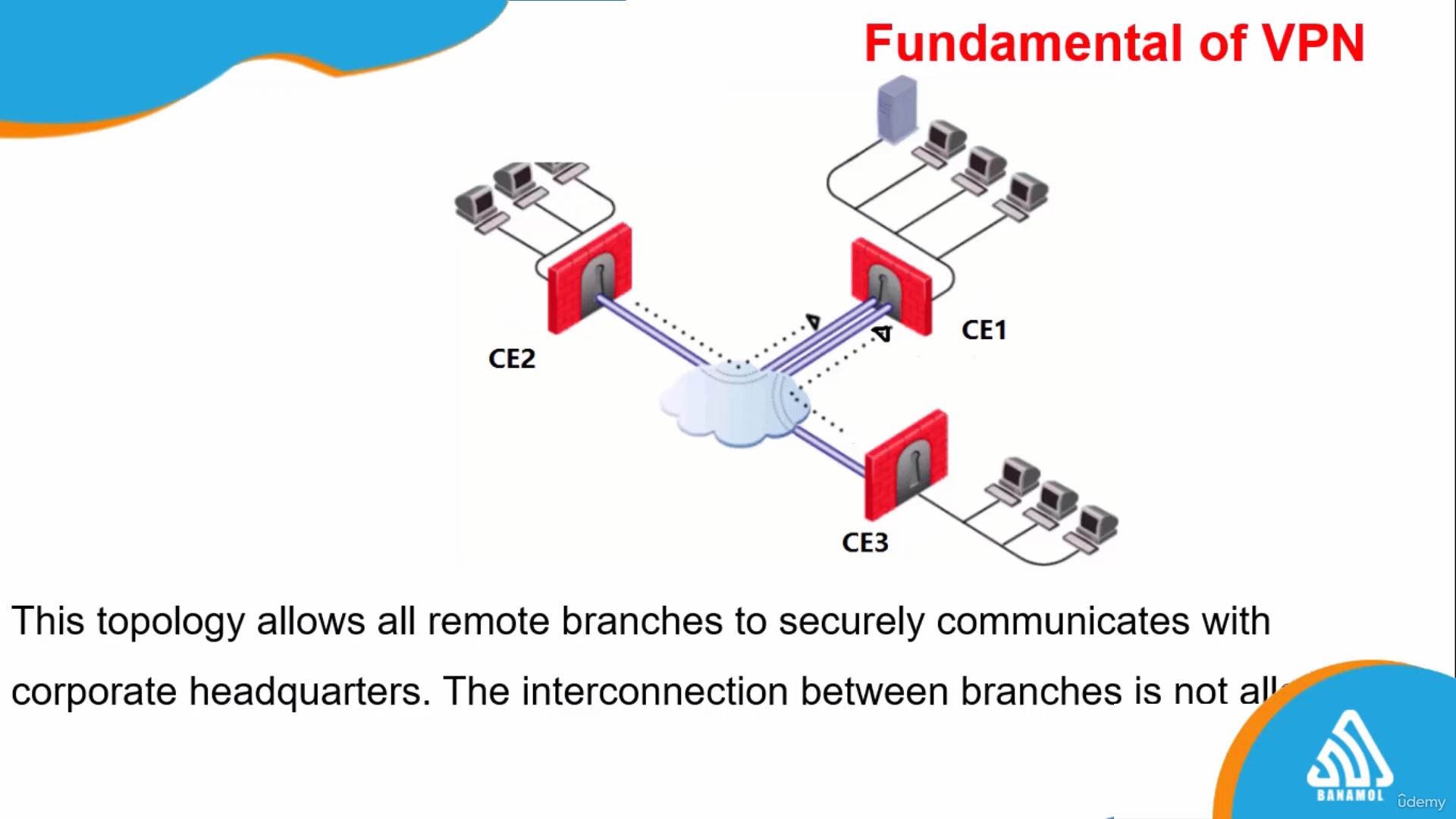
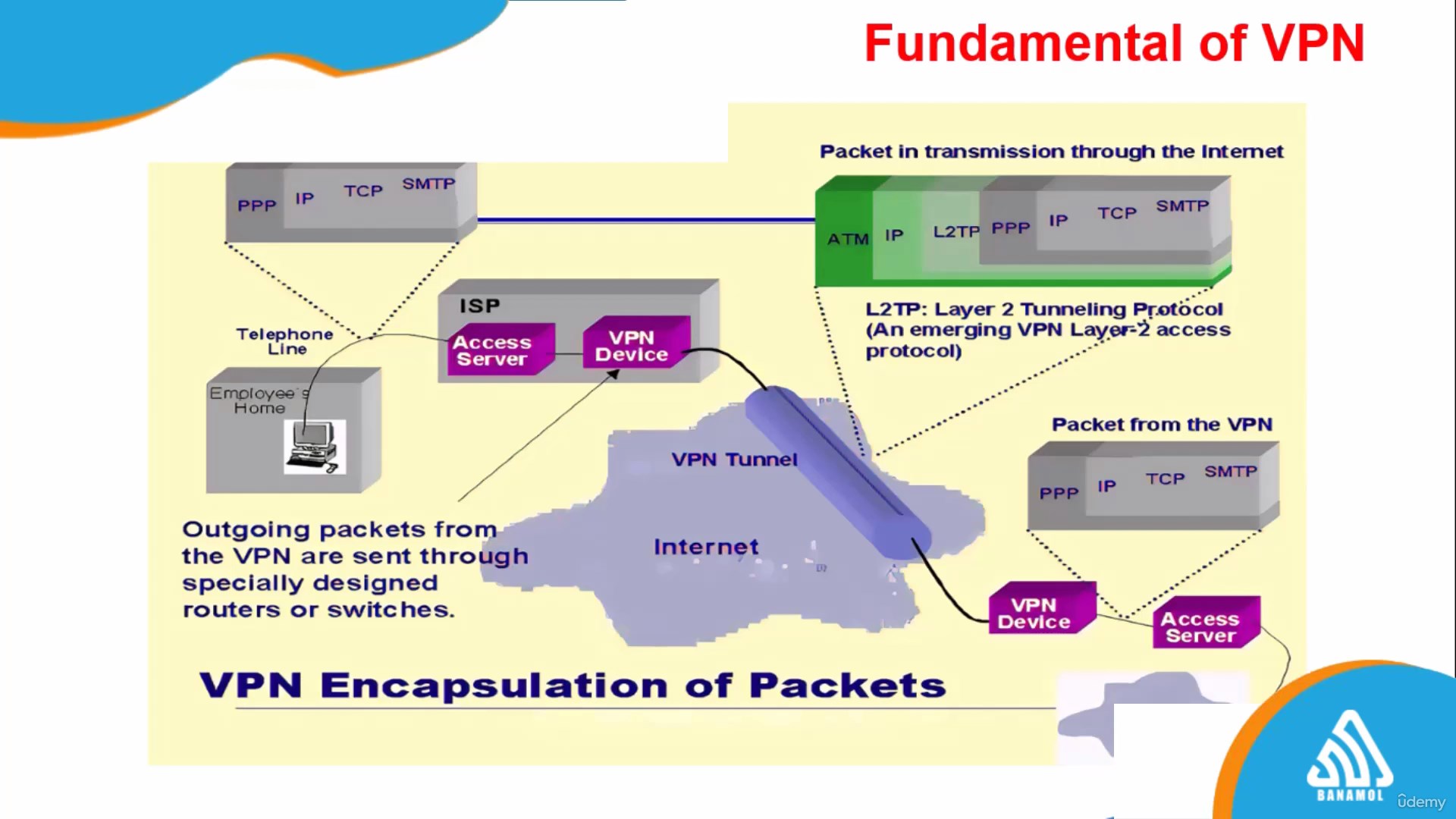
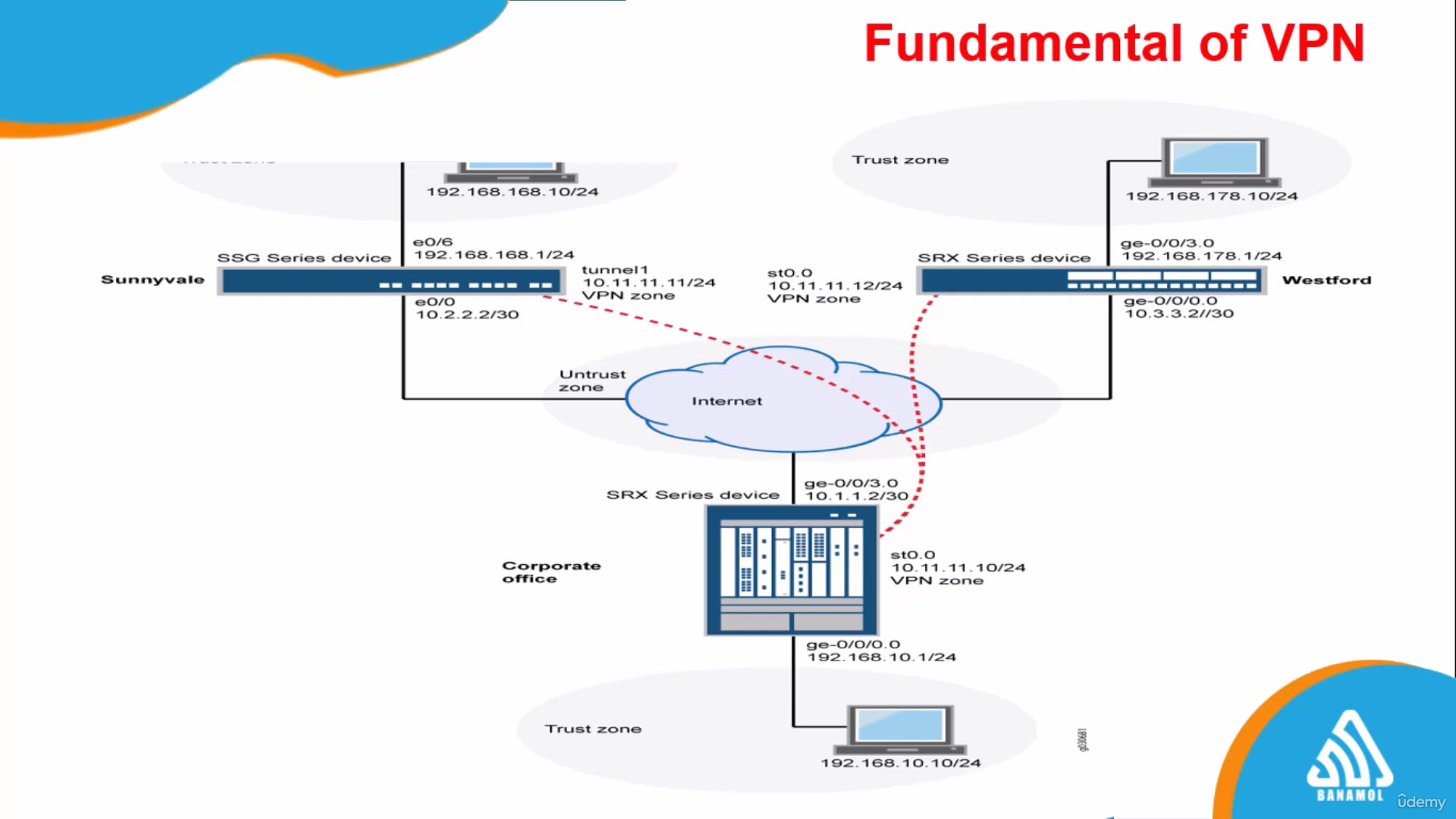
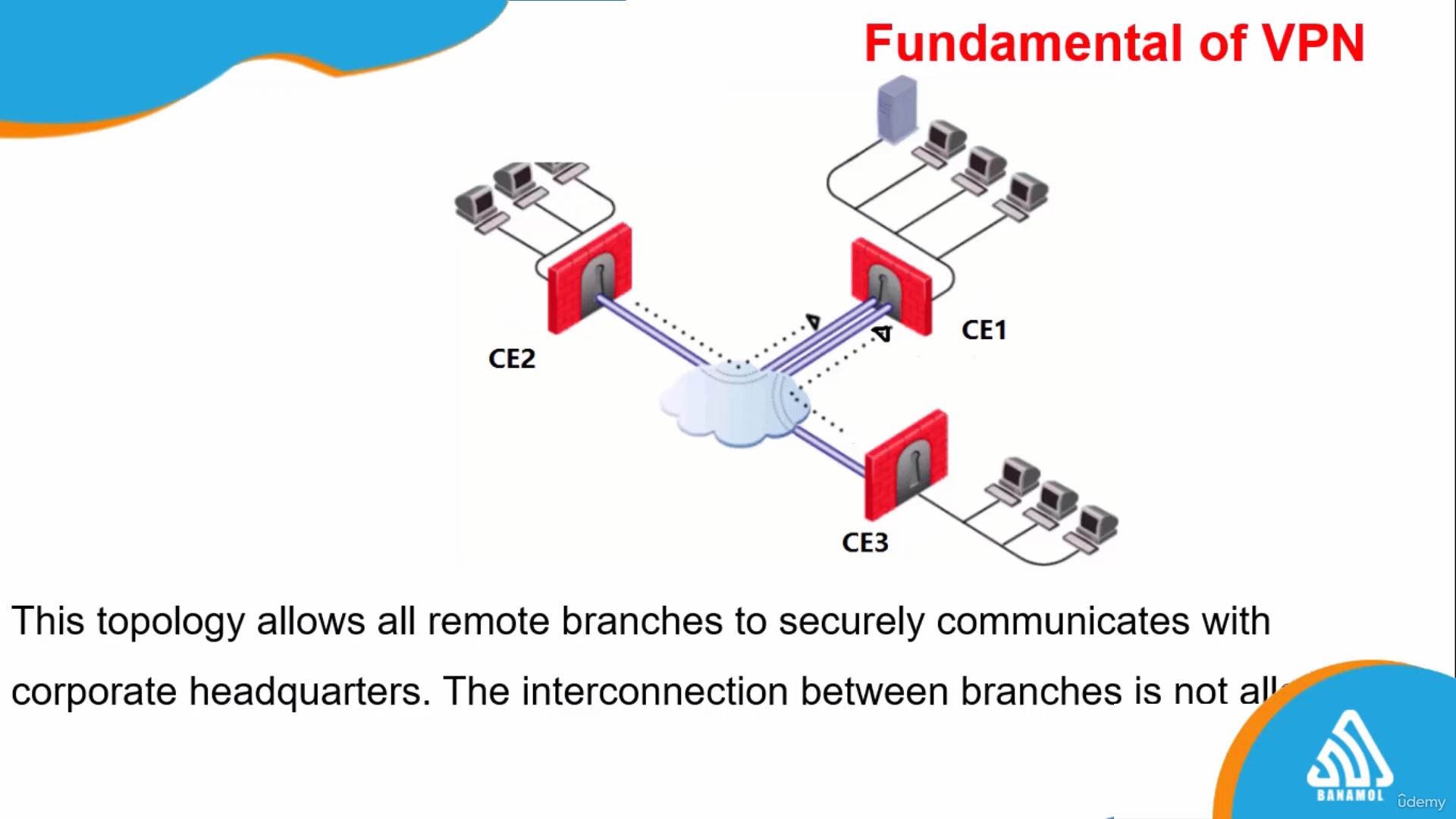
Practical mini-projects such as implementing Snort on Linux platforms, configuring VPNs, and setting up firewalls will ensure that you have hands-on experience in applying what you’ve learned. This course is perfect for those looking to step into the field of cybersecurity or professionals aiming to deepen their knowledge of network defense.
By the end of this course, you will be proficient in the techniques and tools necessary for safeguarding networks against evolving cyber threats, positioning you as a valuable asset in the cybersecurity domain. Whether you're just starting out or looking to update your skills, this course will provide a comprehensive understanding of the essential aspects of network defense.
Over the span of several focused sessions, you will delve into critical areas including identification processes, authentication methods, and authorization procedures. Learn about physical security controls to combat potential attack vectors, and gain in-depth knowledge of technical controls such as firewalls, intrusion detection systems (IDS), intrusion prevention systems (IPS), proxy servers, and the crucial roles they play in network segmentation.
Further enhancing your expertise, the course covers virtualization and cloud computing security, highlighting the benefits and best practices of cloud services. You will also navigate through the complexities of wireless network security, IoT device protection, and the pivotal elements of cryptography and public key infrastructure (PKI).
Practical mini-projects such as implementing Snort on Linux platforms, configuring VPNs, and setting up firewalls will ensure that you have hands-on experience in applying what you’ve learned. This course is perfect for those looking to step into the field of cybersecurity or professionals aiming to deepen their knowledge of network defense.
By the end of this course, you will be proficient in the techniques and tools necessary for safeguarding networks against evolving cyber threats, positioning you as a valuable asset in the cybersecurity domain. Whether you're just starting out or looking to update your skills, this course will provide a comprehensive understanding of the essential aspects of network defense.
Who this course is for:
IT professionals looking to specialize in network security.
Beginners interested in a cybersecurity career.
System administrators aiming to enhance their security skills.
Students studying computer science or related fields.
Business owners needing to secure their network environments.
Hobbyists and tech enthusiasts eager to learn about network defense.
Download
You must be registered for see links
You must be registered for see links
You must be registered for see links
