- Downloaded
- 135.2 GB
- Uploaded
- 13.1 TB
- Ratio
- 99.14
- Seedbonus
- 262,793
- Upload Count
- 265 (300)
Member for 9 years
[udemy] Cloud Security Complete Course

MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz
Language: English | Size: 2.00 GB | Duration: 3h 7m
Learn Security in Cloud Systems with Examples
on AWS, GOOGLE, MICROSOFT Cloud Services

MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz
Language: English | Size: 2.00 GB | Duration: 3h 7m
Learn Security in Cloud Systems with Examples
on AWS, GOOGLE, MICROSOFT Cloud Services
What you'll learn
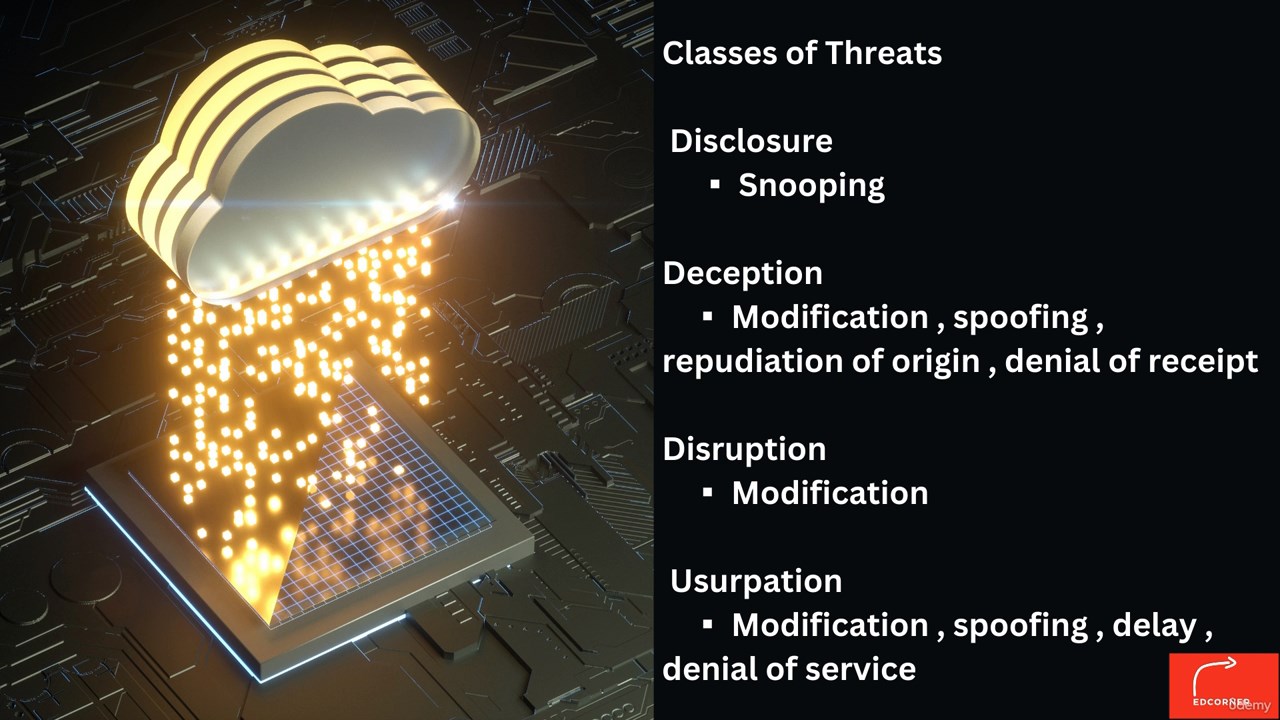
Security Basic Components, Security Attacks, Classes of Threats
Policies and Mechanisms, Goals of Security in Cloud Computing, Trust and Assumptions in Cloud Security
Cloud Security Mechanisms, Assurance, Passive attacks, Active attacks
Gartner's Seven Cloud Computing, Role of Security, Network security
Research Paper amazon ec2
New Risks in Cloud, Multi - tenancy, Attack Model, Threat Model
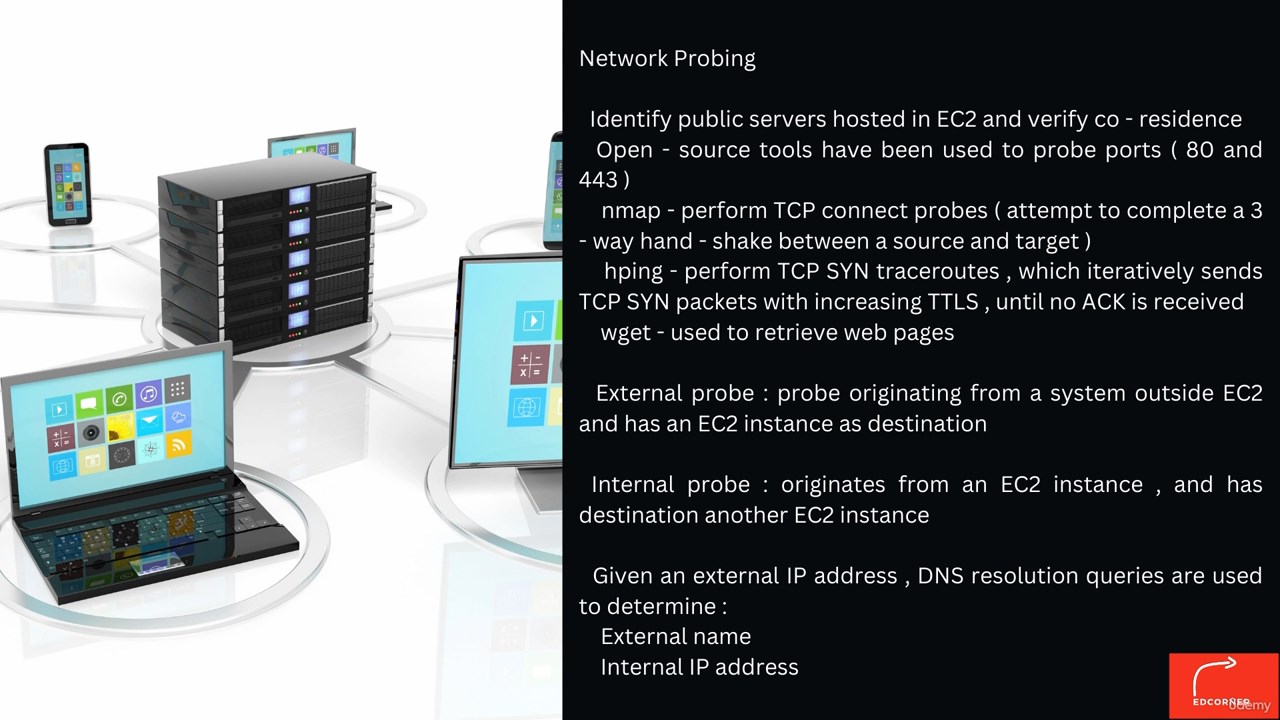
Amazon EC2 Service , Network Probing, Survey Public Servers on EC2, Instance Placement Parameters
Determining Co - residence, Security Issues in Cloud Computing, SaaS Cloud - based Collaboration
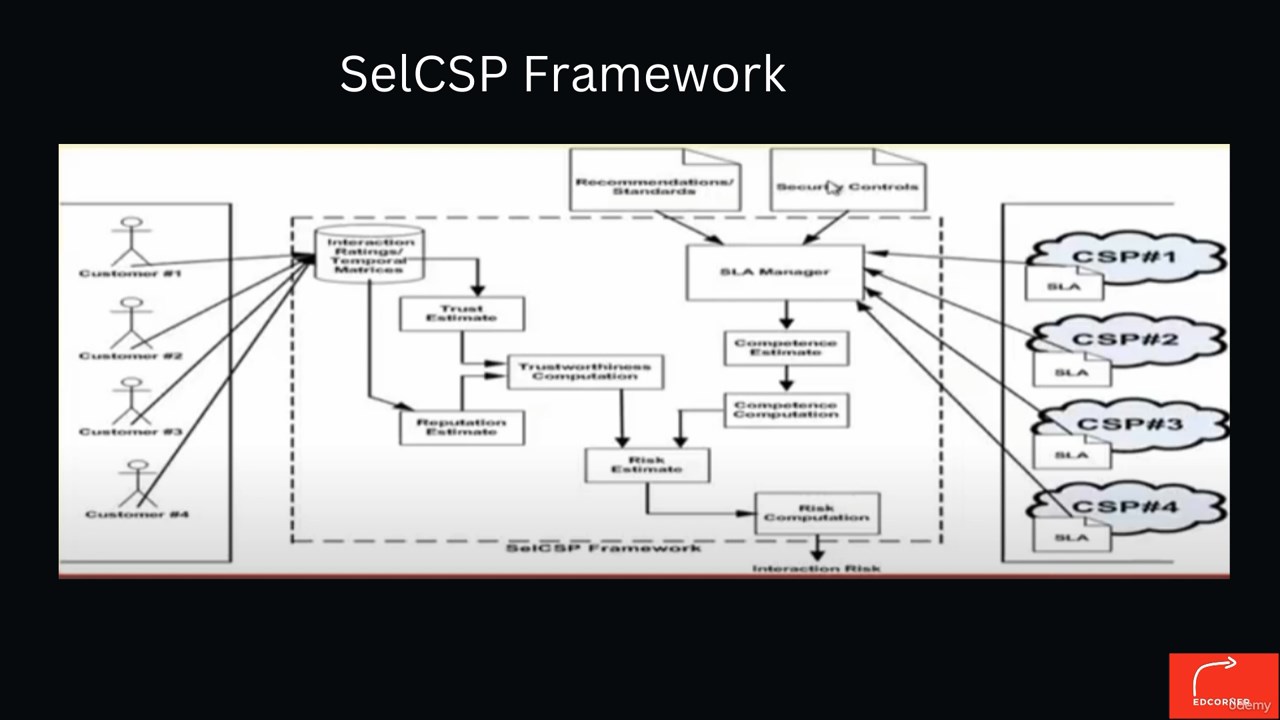
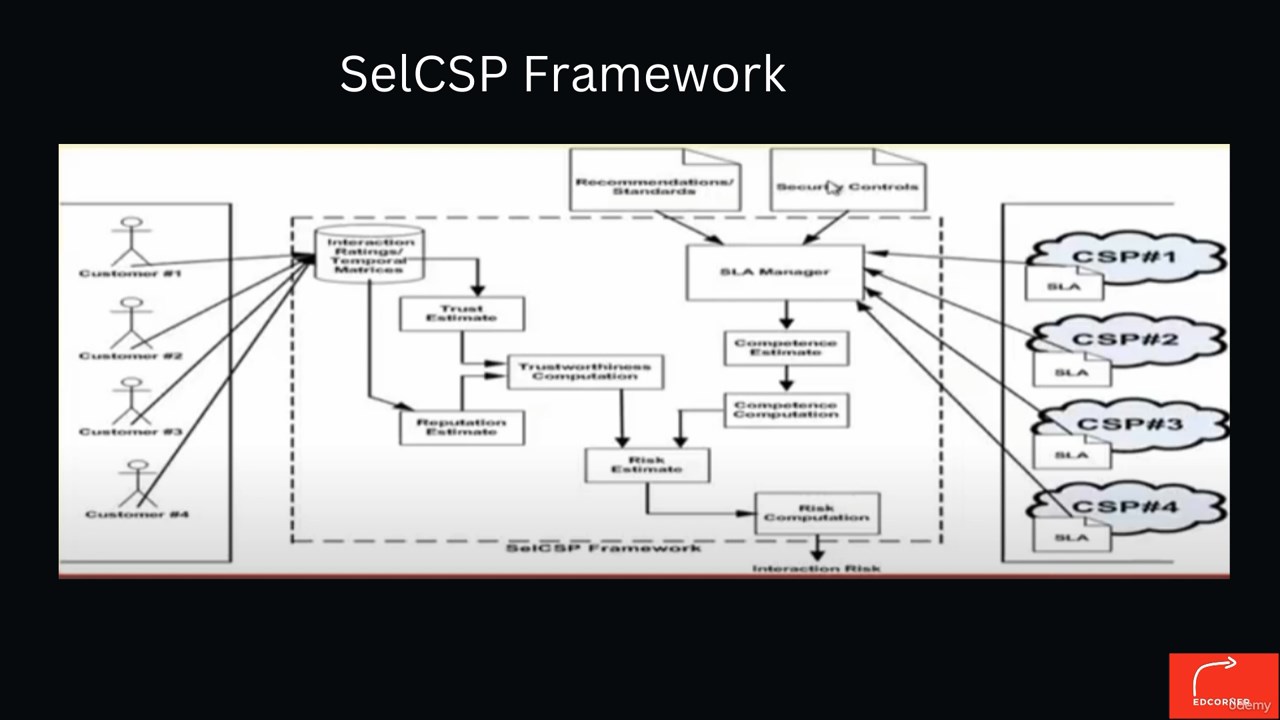
A distributed secure collaboration fra ... SelCSP Framework in detail, Risk - based Access Control ( RAC )
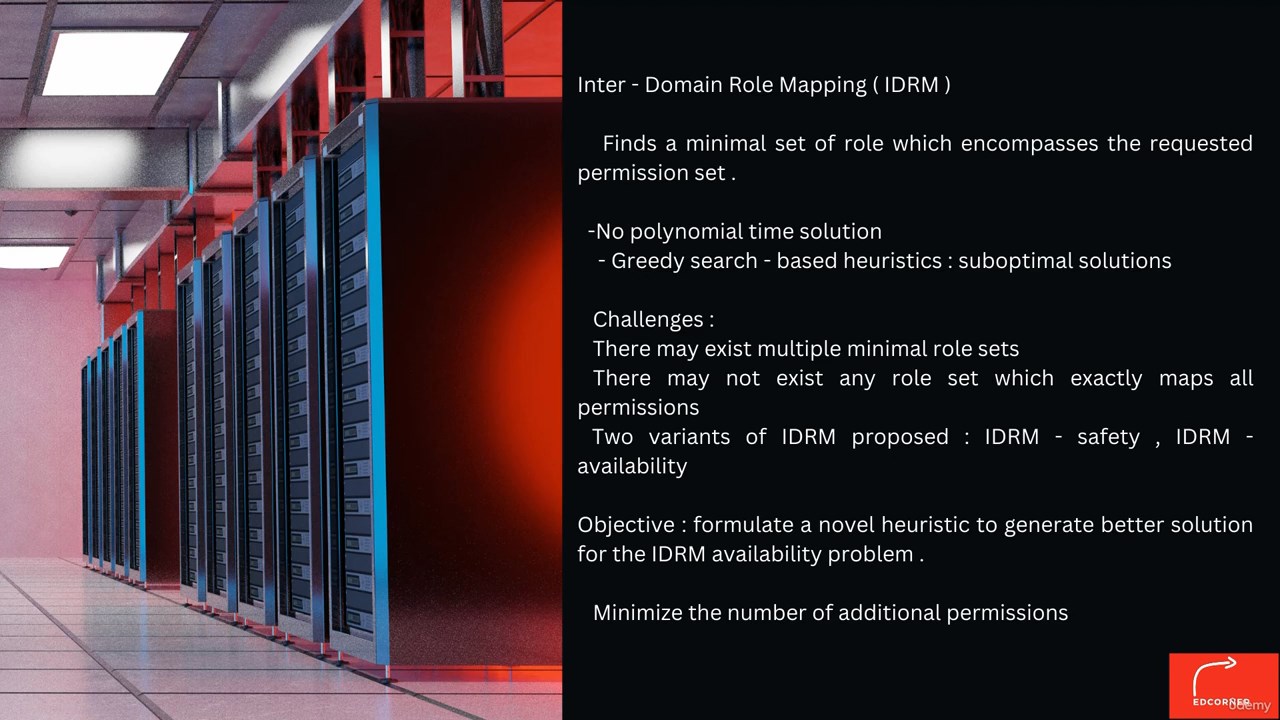
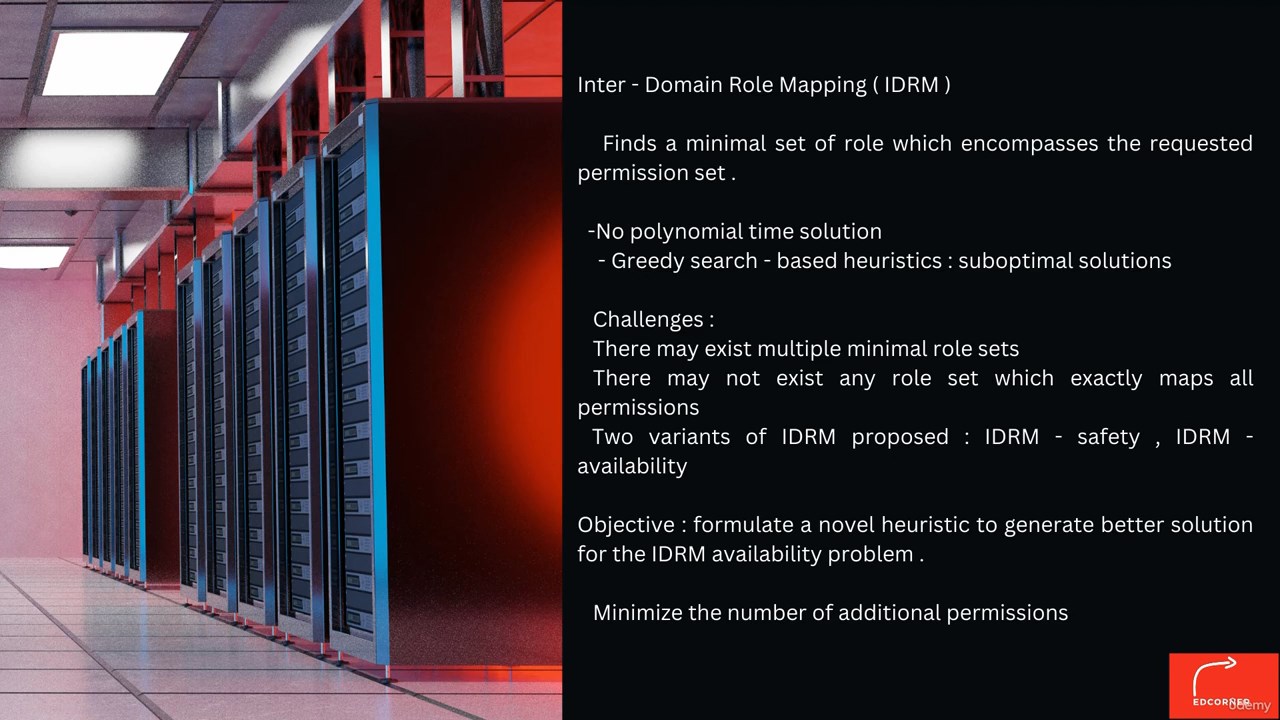
Distributed RAC using Fuzzy Inference, Inter - Domain Role Mapping ( IDRM ), Distributed Role Mapping Framework
Conflict Detection, Conflict Removal, Importance of QoS, Objectives Qos
Different Approaches for selecting CSP, CUSTOMER QoS PARAMETERS, Provider Selection
Case Study
Future Scope
Top Critical Points for AWS Cloud Security
Top critical points for Google cloud and Microsoft cloud Security
Requirements
Little understanding of Cloud Computing.
Who this course is for:
Information Technology enthusiasts that desire to learn the foundations of modern cloud security






Download
Security Basic Components, Security Attacks, Classes of Threats
Policies and Mechanisms, Goals of Security in Cloud Computing, Trust and Assumptions in Cloud Security
Cloud Security Mechanisms, Assurance, Passive attacks, Active attacks
Gartner's Seven Cloud Computing, Role of Security, Network security
Research Paper amazon ec2
New Risks in Cloud, Multi - tenancy, Attack Model, Threat Model
Amazon EC2 Service , Network Probing, Survey Public Servers on EC2, Instance Placement Parameters
Determining Co - residence, Security Issues in Cloud Computing, SaaS Cloud - based Collaboration
A distributed secure collaboration fra ... SelCSP Framework in detail, Risk - based Access Control ( RAC )
Distributed RAC using Fuzzy Inference, Inter - Domain Role Mapping ( IDRM ), Distributed Role Mapping Framework
Conflict Detection, Conflict Removal, Importance of QoS, Objectives Qos
Different Approaches for selecting CSP, CUSTOMER QoS PARAMETERS, Provider Selection
Case Study
Future Scope
Top Critical Points for AWS Cloud Security
Top critical points for Google cloud and Microsoft cloud Security
Requirements
Little understanding of Cloud Computing.
Cloud computing has revolutionized the way businesses operate, offering on-demand access to computing resources at scale. However, with the increase in cloud adoption, security concerns have emerged as a significant challenge for organizations. This comprehensive course on Cloud Security provides participants with a deep understanding of cloud security, including basic components, attacks, classes of threats, policies, and mechanisms.
The course starts with an introduction to cloud security, which covers the essential aspects of cloud security, including confidentiality, integrity, availability, and accountability. Participants will learn about the different security attacks, including passive and active attacks, and the classes of threats that organizations face in cloud computing environments. The course delves into the importance of security policies and mechanisms and how organizations can use them to protect their data in the cloud.
The course provides an in-depth understanding of the goals of security in cloud computing, which include protecting data, ensuring compliance, maintaining service levels, and minimizing the risk of data breaches. Participants will learn about the trust and assumptions in cloud security, and how organizations can implement cloud security mechanisms to protect their data in the cloud.
The course discusses cloud security assurance, which is the process of ensuring that the cloud service provider is meeting the security requirements of the organization. Participants will learn about the different mechanisms for ensuring cloud security, including third-party audits and certifications.
The course provides an in-depth understanding of the different types of security attacks, including passive attacks, which involve eavesdropping and monitoring, and active attacks, which involve modifying or manipulating data. Participants will learn about the Gartner's Seven Cloud Computing, which include the role of security in cloud computing and network security. They will also learn about the research paper on Amazon EC2 and the new risks in the cloud, such as multi-tenancy and the attack model and threat model.
The course addresses various queries, including Amazon EC2 Service, network probing, survey public servers on EC2, instance placement parameters, determining co-residence, and security issues in cloud computing. Participants will learn about SaaS cloud-based collaboration and the SelCSP framework, which is a distributed secure collaboration framework. The course also covers risk-based access control (RAC), distributed RAC using fuzzy inference, inter-domain role mapping (IDRM), distributed role mapping framework, conflict detection, and conflict removal.
The course provides an in-depth understanding of the importance of Quality of Service (QoS) and different approaches for selecting a CSP. Participants will learn about the customer QoS parameters and provider selection. The course provides a case study and future scope of cloud security. It also covers the top critical points for AWS Cloud Security, Google Cloud, and Microsoft Cloud Security.
Overall, this course provides participants with the knowledge and skills to identify and mitigate security threats and attacks in the cloud. They will be able to implement appropriate security policies and mechanisms to secure cloud computing systems, including multi-tenant environments. The course also prepares participants to apply best practices for selecting a cloud service provider and implementing risk-based access control.
In conclusion, this course is essential for professionals working in cloud computing and those who want to learn more about cloud security. It provides a comprehensive understanding of cloud security and equips participants with the knowledge and skills needed to secure cloud computing systems effectively. The course covers various topics, including security attacks, classes of threats, policies, and mechanisms, and addresses different queries, including Amazon EC2 service, network probing, and instance placement parameters. The course provides a case study and future scope of cloud security and covers the top critical points for AWS Cloud Security, Google Cloud, and Microsoft Cloud Security. Participants will gain an in-depth understanding of cloud security, which will help them secure cloud computing systems effectively.
The course starts with an introduction to cloud security, which covers the essential aspects of cloud security, including confidentiality, integrity, availability, and accountability. Participants will learn about the different security attacks, including passive and active attacks, and the classes of threats that organizations face in cloud computing environments. The course delves into the importance of security policies and mechanisms and how organizations can use them to protect their data in the cloud.
The course provides an in-depth understanding of the goals of security in cloud computing, which include protecting data, ensuring compliance, maintaining service levels, and minimizing the risk of data breaches. Participants will learn about the trust and assumptions in cloud security, and how organizations can implement cloud security mechanisms to protect their data in the cloud.
The course discusses cloud security assurance, which is the process of ensuring that the cloud service provider is meeting the security requirements of the organization. Participants will learn about the different mechanisms for ensuring cloud security, including third-party audits and certifications.
The course provides an in-depth understanding of the different types of security attacks, including passive attacks, which involve eavesdropping and monitoring, and active attacks, which involve modifying or manipulating data. Participants will learn about the Gartner's Seven Cloud Computing, which include the role of security in cloud computing and network security. They will also learn about the research paper on Amazon EC2 and the new risks in the cloud, such as multi-tenancy and the attack model and threat model.
The course addresses various queries, including Amazon EC2 Service, network probing, survey public servers on EC2, instance placement parameters, determining co-residence, and security issues in cloud computing. Participants will learn about SaaS cloud-based collaboration and the SelCSP framework, which is a distributed secure collaboration framework. The course also covers risk-based access control (RAC), distributed RAC using fuzzy inference, inter-domain role mapping (IDRM), distributed role mapping framework, conflict detection, and conflict removal.
The course provides an in-depth understanding of the importance of Quality of Service (QoS) and different approaches for selecting a CSP. Participants will learn about the customer QoS parameters and provider selection. The course provides a case study and future scope of cloud security. It also covers the top critical points for AWS Cloud Security, Google Cloud, and Microsoft Cloud Security.
Overall, this course provides participants with the knowledge and skills to identify and mitigate security threats and attacks in the cloud. They will be able to implement appropriate security policies and mechanisms to secure cloud computing systems, including multi-tenant environments. The course also prepares participants to apply best practices for selecting a cloud service provider and implementing risk-based access control.
In conclusion, this course is essential for professionals working in cloud computing and those who want to learn more about cloud security. It provides a comprehensive understanding of cloud security and equips participants with the knowledge and skills needed to secure cloud computing systems effectively. The course covers various topics, including security attacks, classes of threats, policies, and mechanisms, and addresses different queries, including Amazon EC2 service, network probing, and instance placement parameters. The course provides a case study and future scope of cloud security and covers the top critical points for AWS Cloud Security, Google Cloud, and Microsoft Cloud Security. Participants will gain an in-depth understanding of cloud security, which will help them secure cloud computing systems effectively.
Who this course is for:
Information Technology enthusiasts that desire to learn the foundations of modern cloud security






Download
You must be registered for see links
You must be registered for see links
You must be registered for see links
